Introducing Agentic Data Access: The Next Era of Data Provisioning
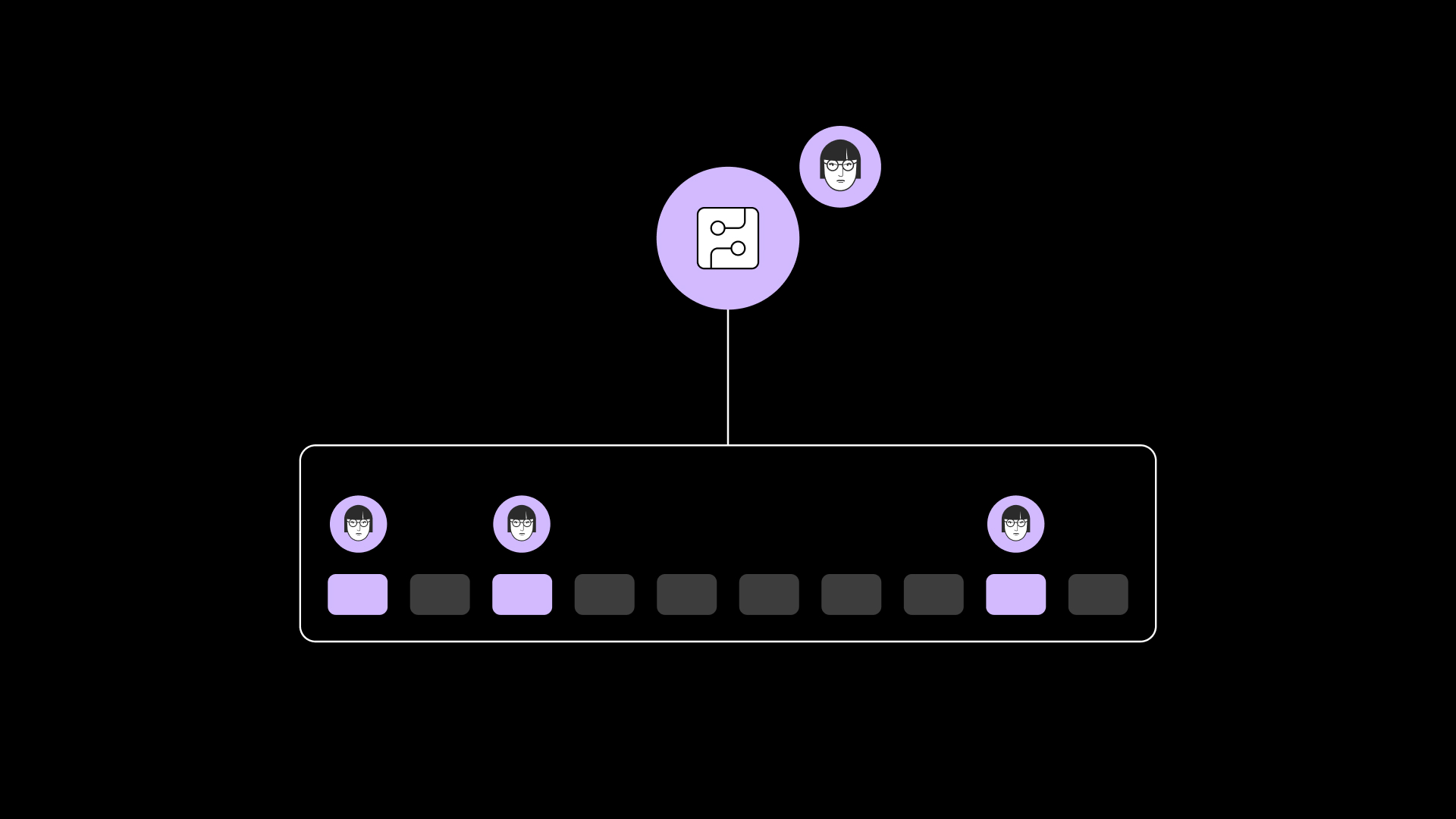
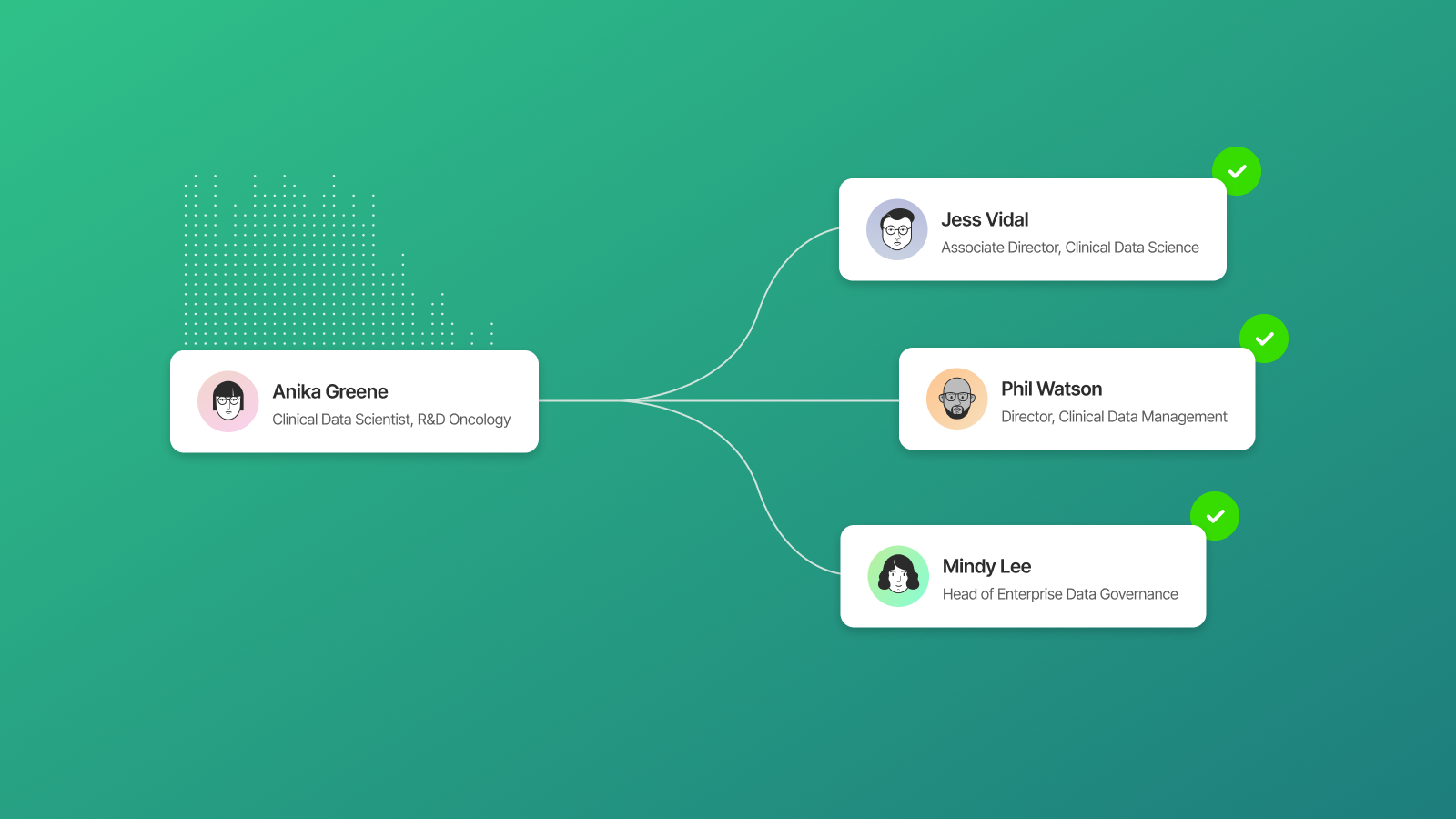
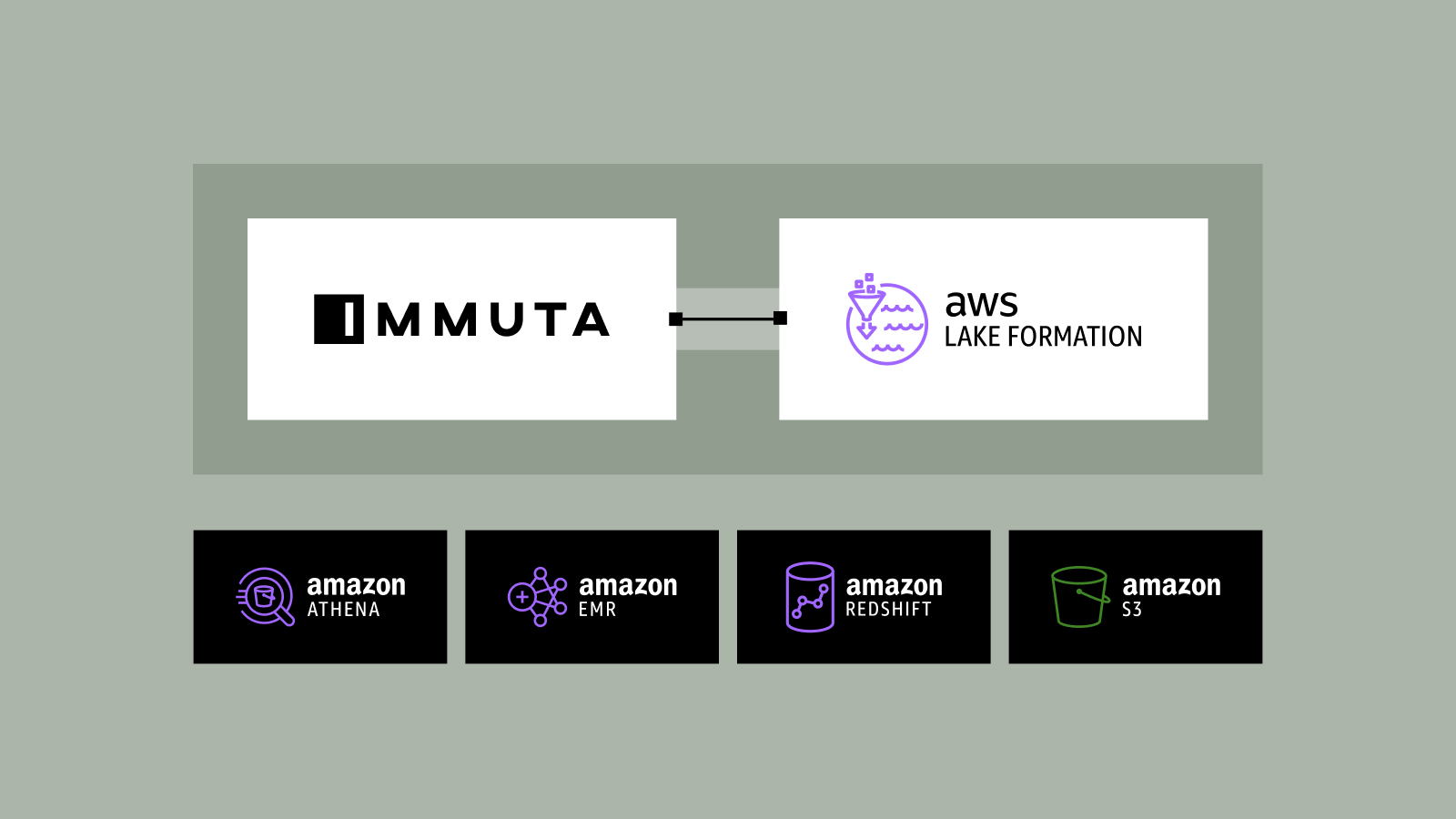
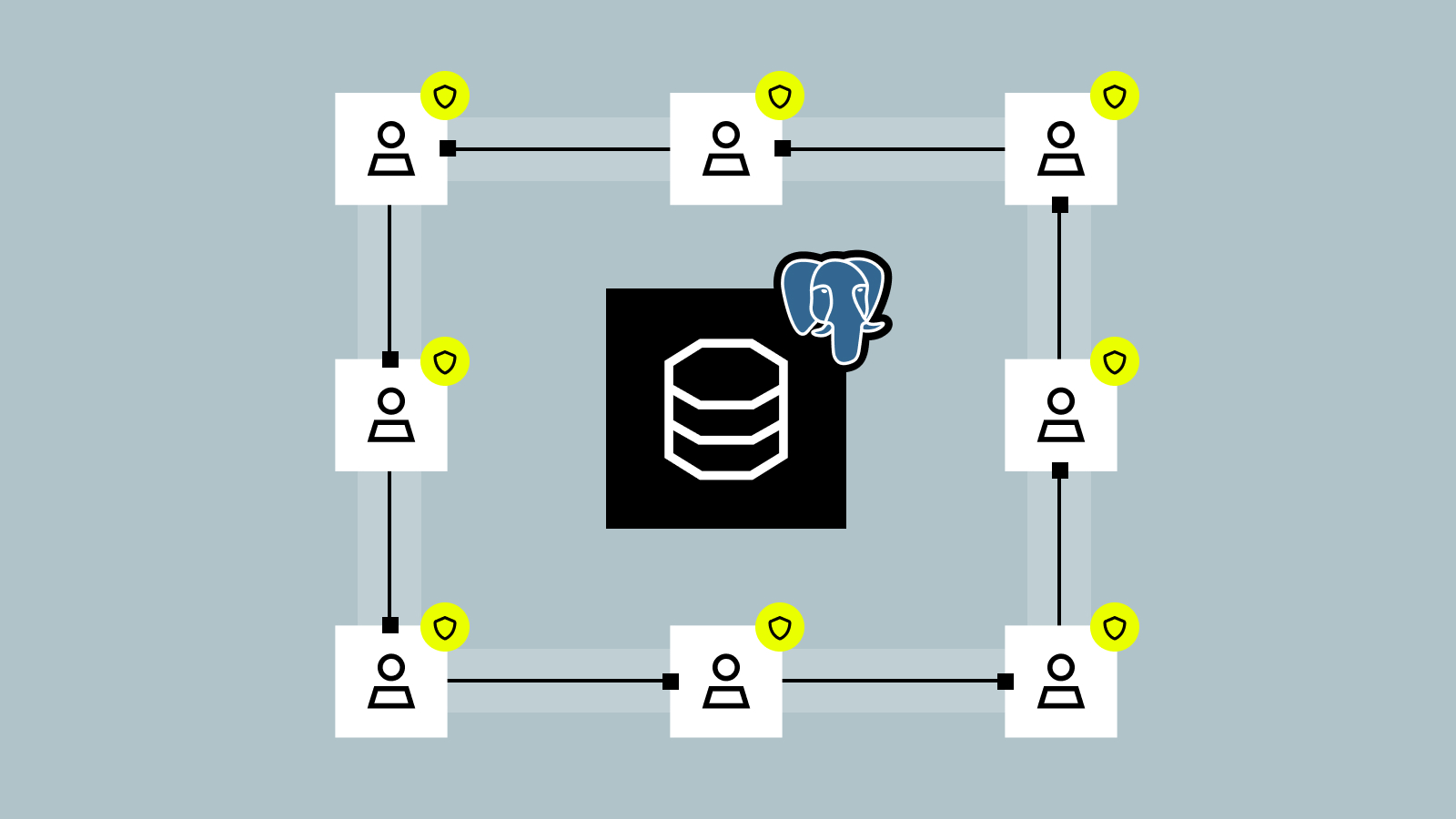
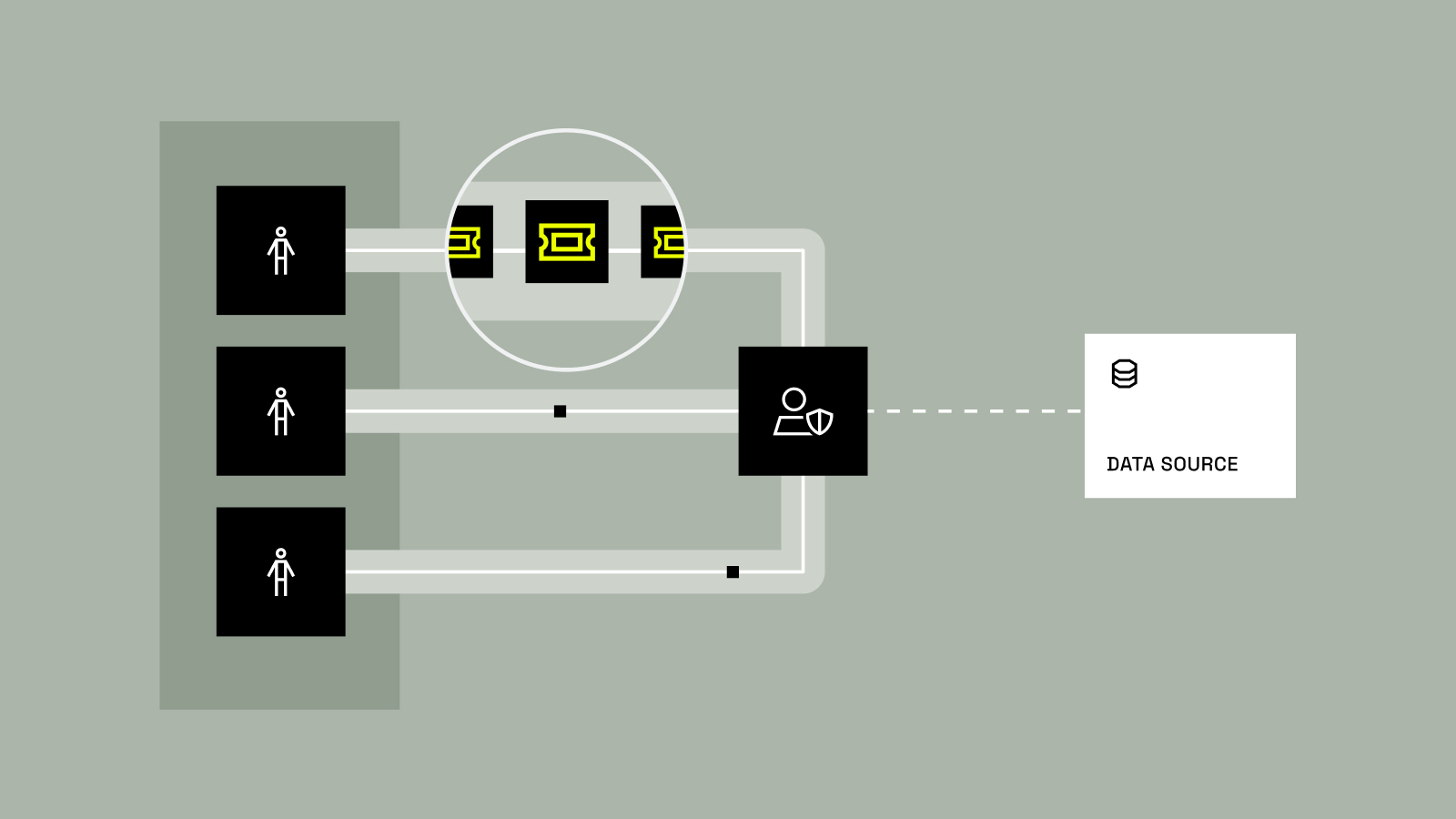
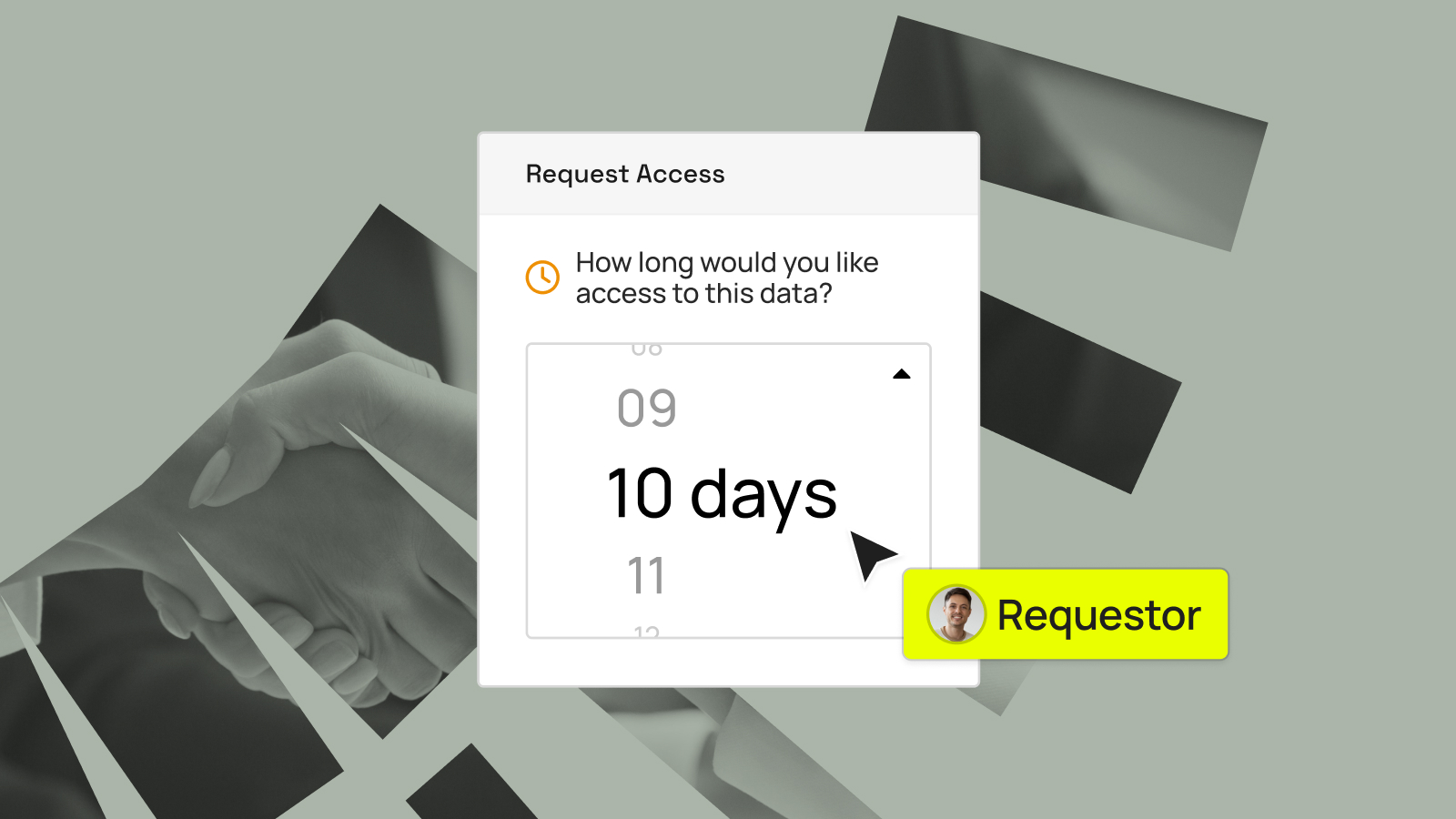
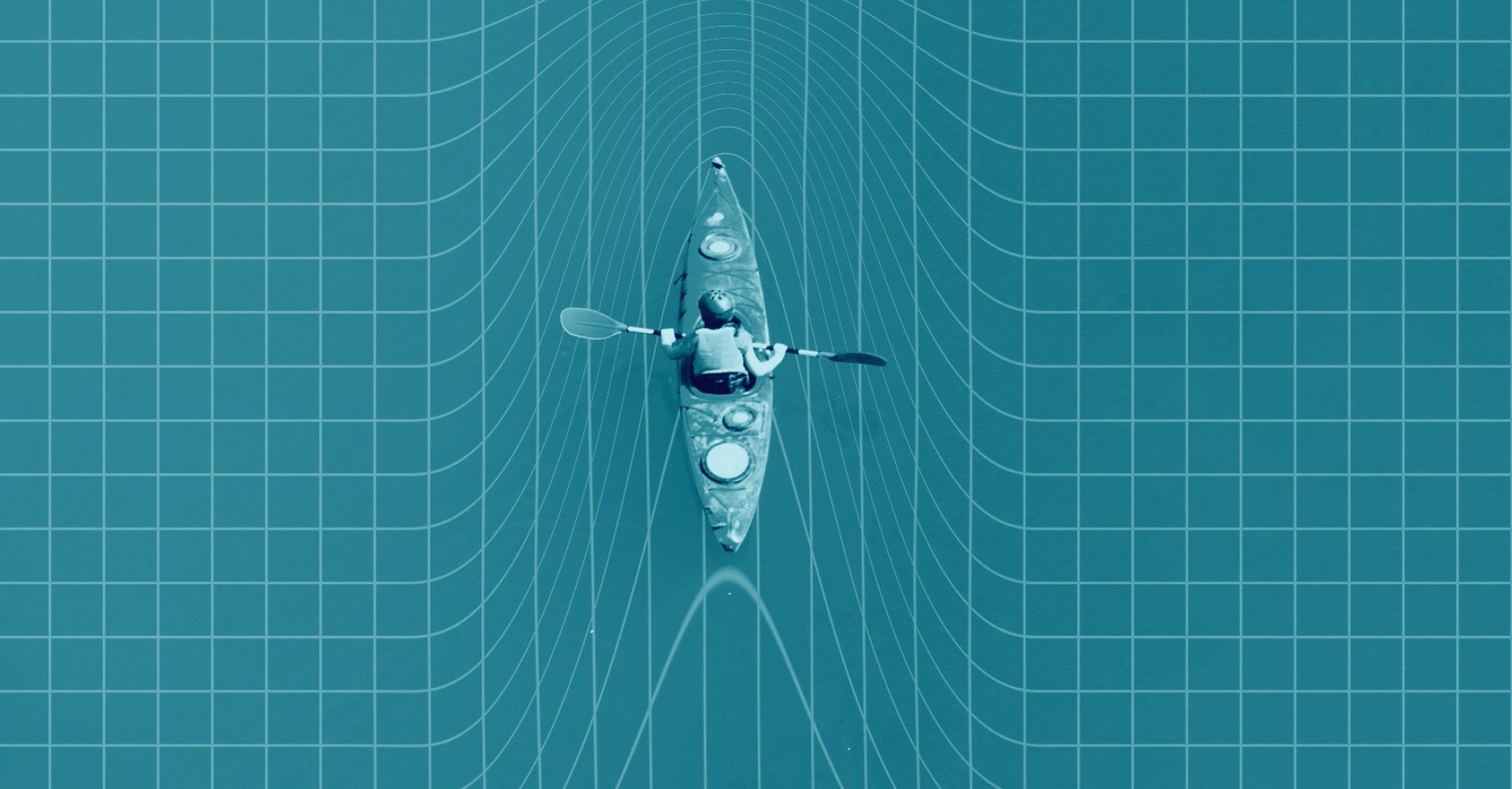
For years, enterprise data access was built around a simple assumption: the requester was human. That world is changing fast. AI agents are moving from copilots to active participants in enterprise workflows. They don’t just retrieve answers, they search for data, plan how to answer questions, adapt when they hit...