Immuta for Public Sector
Turning mission-critical data into action.
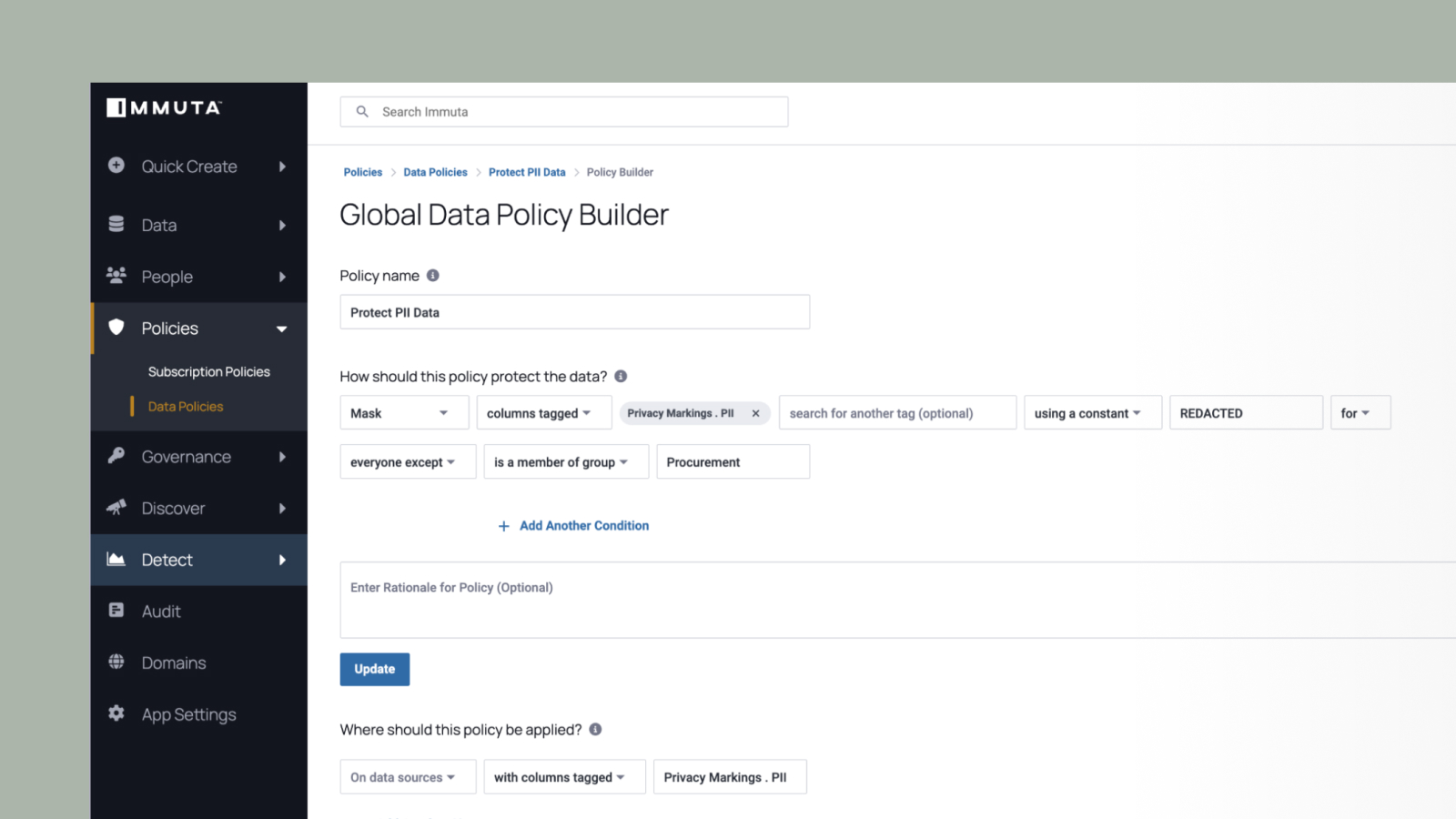
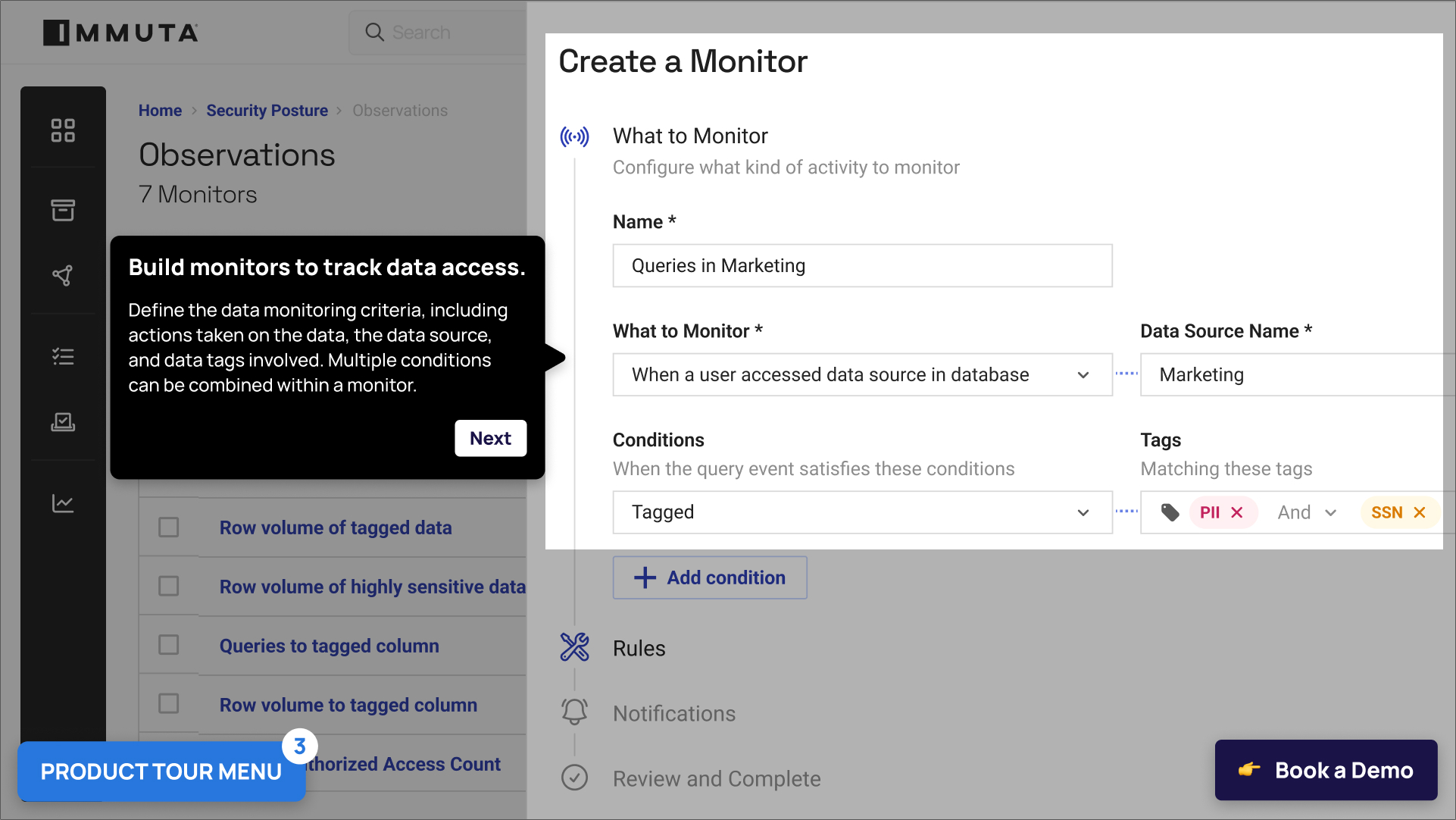
Public sector agencies require data accessibility and control. Born out of the US Intelligence Community, Immuta protects the world’s most sensitive data, and in turn, national security, economic growth, and citizens’ wellbeing.