What “Continuous Compliance” Means in the AI Era
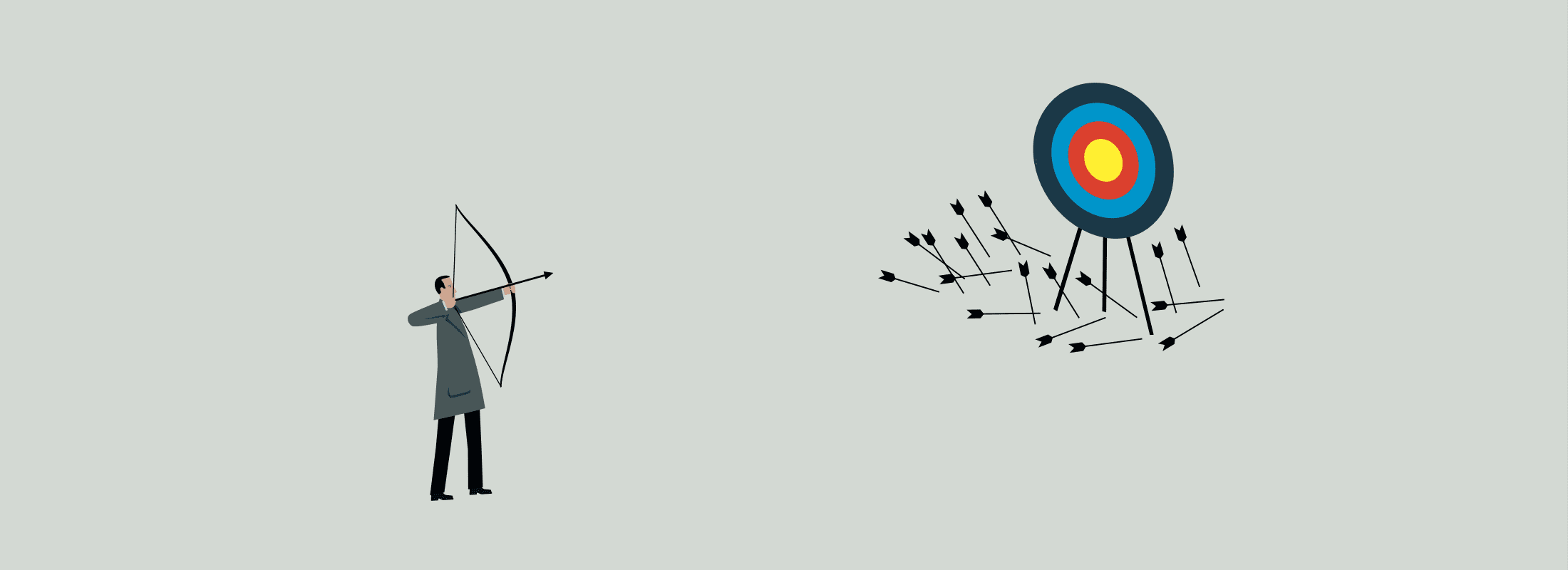
For years, compliance has been treated like a recurring exercise: something teams prepare for, complete, and then set aside until the next review cycle. That model made sense when access patterns were relatively predictable and tied to static roles. Our modern data environments look nothing like that. Access is continuous,...