Making Agentic Data Access Practical and Safe
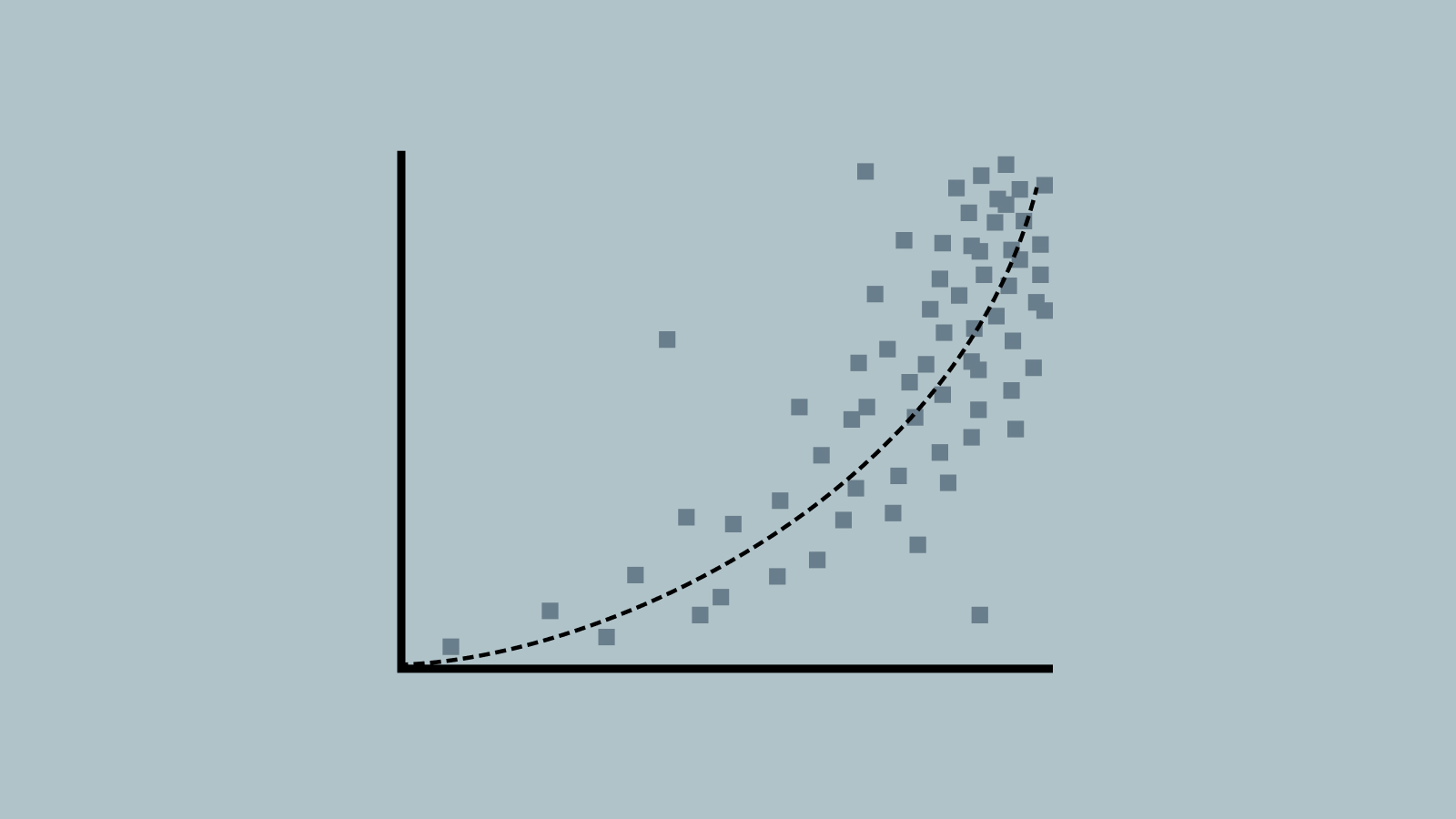
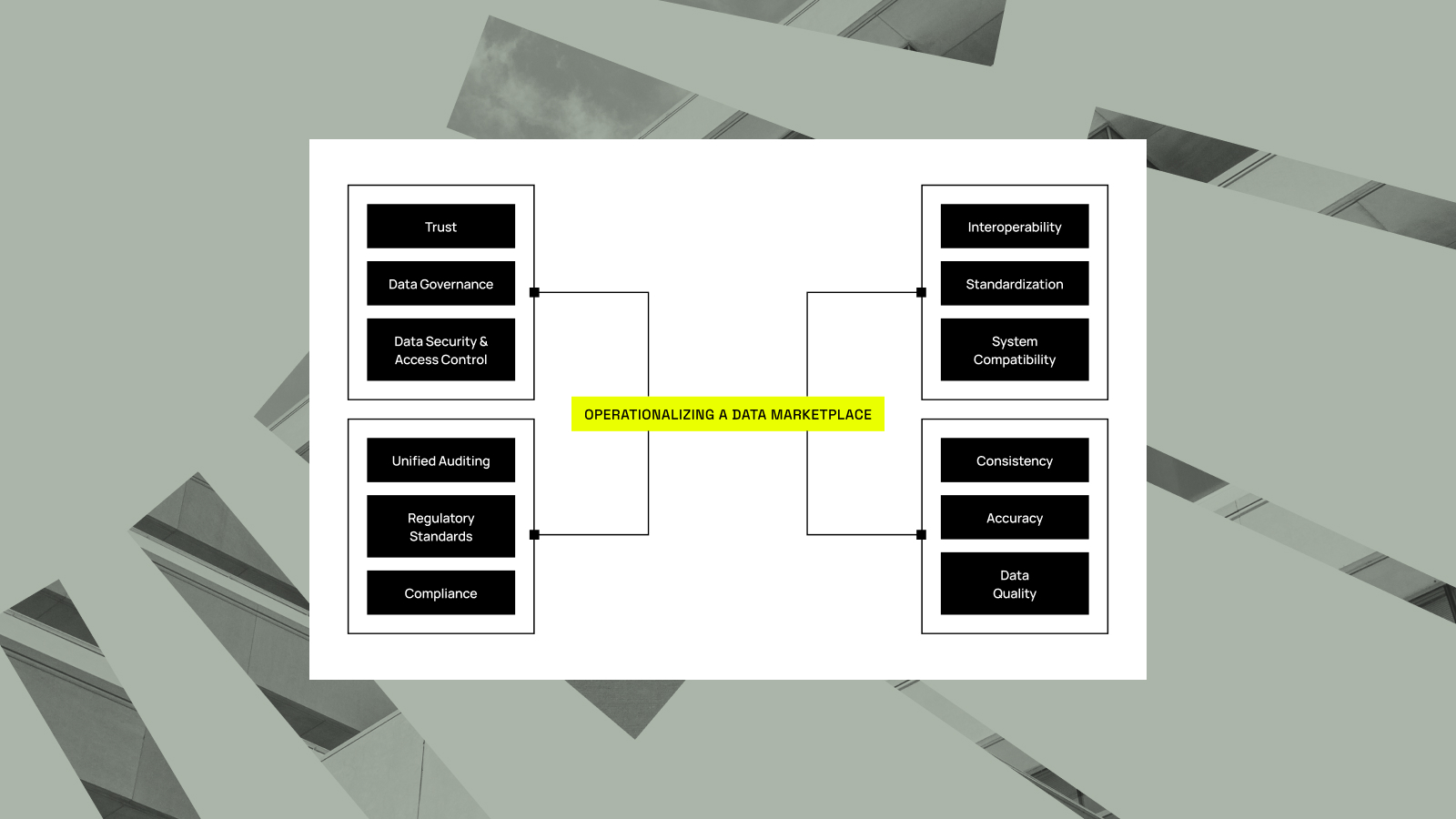
Most organizations know AI agents are coming for their data. Not in a threatening way, but in the practical, inevitable sense: as enterprises roll out AI-assisted workflows, the number of non-human identities requesting access to enterprise data is growing fast. The question isn’t whether to prepare. It’s whether you can....