2022 Data Access & Analytics Trendbook
Expert perspectives on where data use is heading

Immuta’s latest release is here, and we are excited to share the new features and integrations we’ve been working on:
Let’s explore these features in detail.
As the use of Google BigQuery continues to grow globally, enabling secure data access is key to ensuring that only the right people have access to the right data.
Immuta’s comprehensive approach to fine-grained access control goes beyond table-level controls to cover row-level, column-level, and cell-level security, bolstering the security of users’ BigQuery workloads for even the most sensitive data.
With this release, Immuta now natively integrates with Google BigQuery to provide automated data discovery, dynamic access and security controls, and always-on monitoring and reporting, without being in the data path. This strengthens BigQuery data governance by allowing users to quickly, easily, and securely access and share critical data, while benefiting from seamless interoperability in the Google Cloud ecosystem.
Expert perspectives on where data use is heading
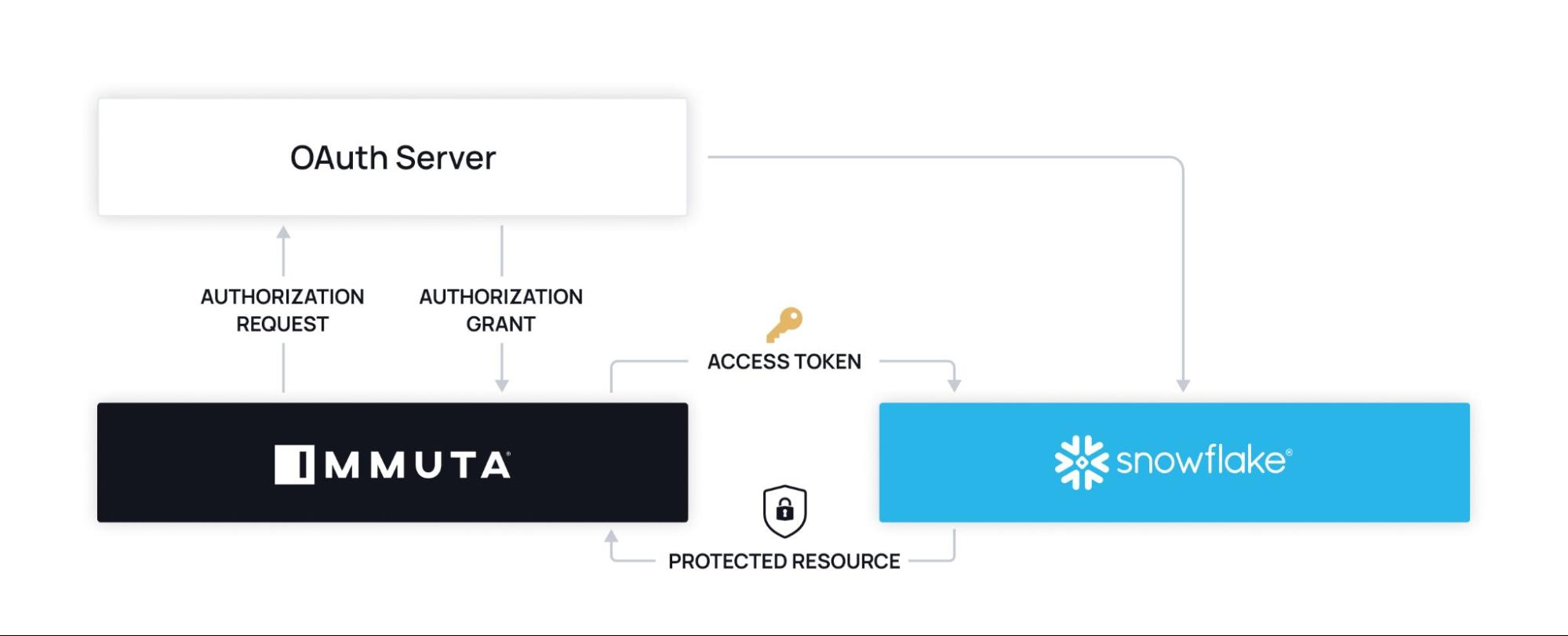
OAuth is one of the most commonly used open-standard protocols for enabling secure delegated access. Since it does not require users to share or store passwords or other login credentials, it is employed by many companies and software vendors.
Immuta now easily integrates with customers’ OAuth provider to facilitate a seamless workflow between Snowflake and Immuta. This simplifies the process of authenticating and authorizing user access, allowing data teams to enable Snowflake data access faster while also meeting corporate security requirements.
Immuta’s Snowflake integration now manages table grants for users per subscription policy, meaning users no longer have to manually grant users table access. Ultimately, this simplifies the management of privileges in Snowflake when using Immuta, and increases data teams’ time and productivity by eliminating the need for manual processes.
This new approach relies on a per-user Role for table grants(complexity is hidden in role hierarchy under a single role for each user), only users subscribed to a data source in Immuta are able to view and query the Snowflake table. Those who are not subscribed are able to neither view nor query it.

Most organizations are seeing exponential growth in the amount of data they store and process in Snowflake. Integrating Immuta with Snowflake provides protection for all data sources, and this release increases its capacity to do so. Immuta now makes it possible to ingest metadata for thousands of tables at scale with API-based progress reporting. This means data teams using Snowflake can increase data collection, storage, and usage at the pace of business, without having to worry about any data falling through the cracks.
The Approve to Promote feature allows customers to bring in data sources into Immuta without affecting the existing access control until they are ready.
Customers with separate Immuta instances per environment can now enable the Approve to Promote feature to manage policies across Dev/UAT/Production environments. This iteration, which is in public preview, improves management of only those access requests that are ready to be reviewed – not the policies on which the author is still iterating. This improves efficiency and reduces confusion by streamlining the policy approval process.
More and more customers are storing audit logs in Amazon S3 so they can be analyzed in tools such as Splunk and Snowflake. Capturing and understanding how data has been accessed, used, and changed is a key requirement for data regulation compliance, so it’s a top priority for many AWS customers.
Immuta’s latest release allows Immuta SaaS customers to export audit data collected in Immuta directly to S3, making it easier to integrate with log monitoring services and data pipelines. The audit log data is structured so it can be processed by standard log data processors and tools. This eliminates the need for any manual processes and ensures that all data activity is tracked and monitored appropriately.
With this feature that is now in public preview, enterprise Databricks customers are able to connect data sources to Immuta without affecting any existing access controls until they are ready. This will allow users to decouple data policy authoring from policy ingest, which reduces the upfront effort required to ensure policies were authored correctly initially.
The rapid pace at which data is being created, collected, stored, and analyzed puts the onus on data teams to ensure their infrastructure is managed securely and efficiently. Immuta’s latest release strengthens data discovery, security, and monitoring for Google BigQuery, Snowflake, and AWS, providing more streamlined processes that allow users to get more value from their data at scale.
Check out Immuta’s self-guided demo to start connecting data sources and building policies.
Innovate faster in every area of your business with workflow-driven solutions for data access governance and data marketplaces.