For years, enterprise data access was built around a simple assumption: the requester was human.
That world is changing fast. AI agents are moving from copilots to active participants in enterprise workflows. They don’t just retrieve answers, they search for data, plan how to answer questions, adapt when they hit roadblocks, and increasingly act on behalf of employees and systems. They run 24/7, generate queries dynamically, move across platforms continuously, and expect access decisions in seconds, not days.
We knew the industry was heading here. What surprised us was the speed.
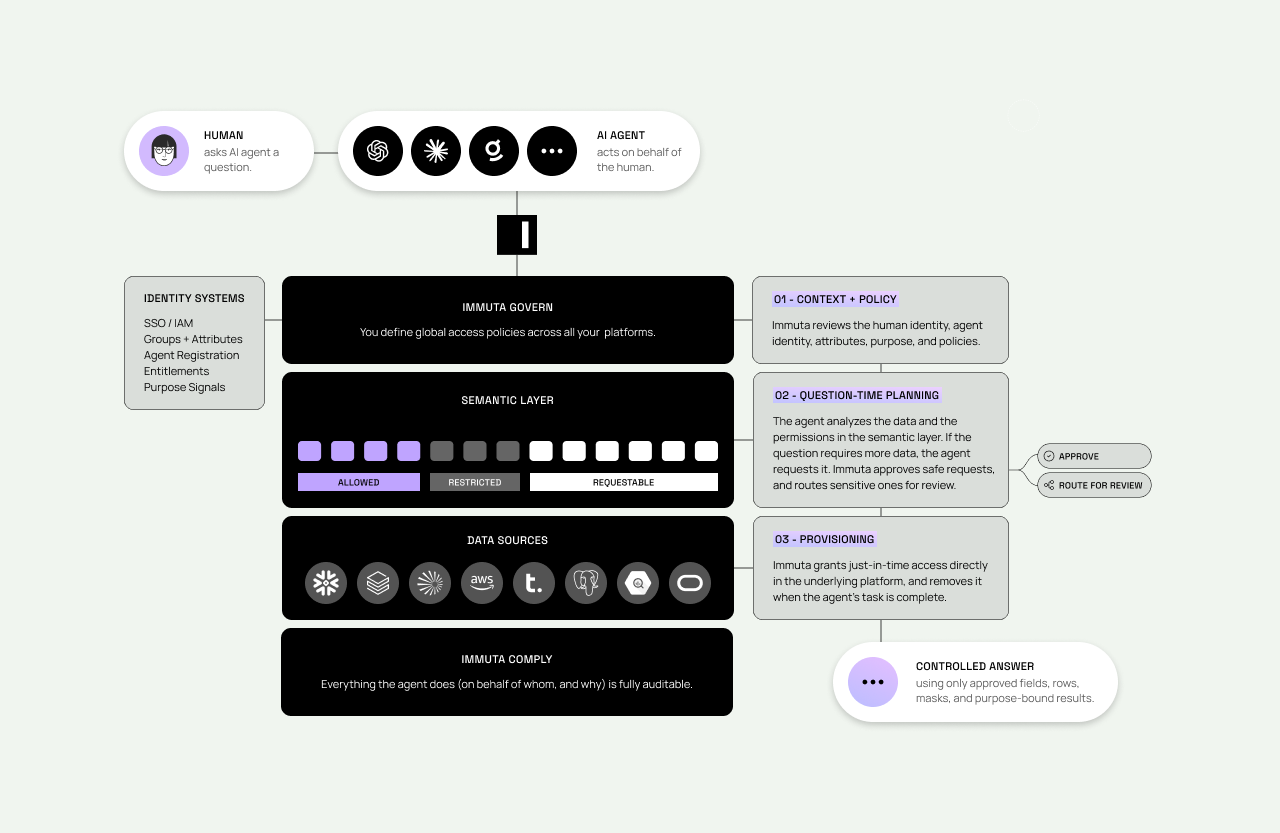
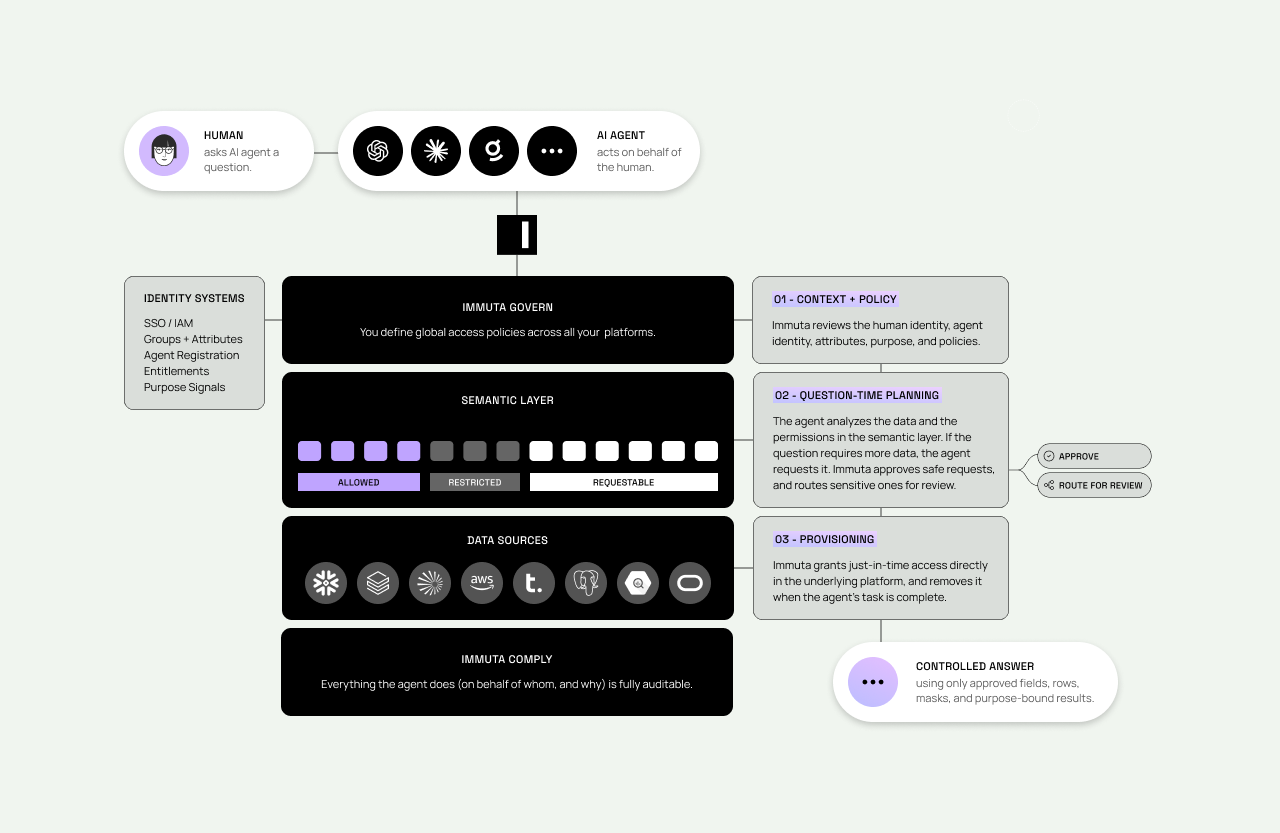
In what feels like no time at all, the market has moved from an era of human-centered governance to one where agents are beginning to operate independently and request access to data on behalf of humans in the flow of work. That shift is exactly why we are announcing Agentic Data Access, a new capability within the Immuta Data Provisioning Platform.
This is a big announcement for Immuta. But it’s not a pivot.
It’s the next logical step in a journey we’ve been building toward for years: from fine-grained data security, to modern data provisioning, to agentic governance at machine speed. Since 2018, as enterprise data moved deeper into the cloud, Immuta has been building a centralized and decoupled authorization layer so policy can be enforced where the data lives, no matter where it lives. Agents did not change that direction. They simply made the need immediate.
The old access model breaks at AI scale
In early AI deployments, many organizations have taken the most obvious path: let the agent log in as the human asking the question. That may be enough for a pilot, but it doesn’t work at enterprise scale.
When agents impersonate humans, every potential AI user needs their specific access to be provisioned across every data system the agent might touch. That creates account sprawl. To keep agents from failing mid-task, organizations often grant broader and longer-lived permissions than the task actually requires. That increases exposure risk and fuels rights inflation. And because the query appears to come from the human identity, audit trails become muddy. Was that data accessed by a person, by an agent acting independently, or by an agent acting on behalf of a person?
Most importantly, impersonation creates human-limited AI. The moment an agent hits a semantic or permission wall, it stalls, even when the right data exists and could potentially be discovered, requested, and provisioned safely.
Human-scale processes also cannot keep up with AI-scale demand. Generative AI has already turned far more people into data consumers. Agentic AI multiplies that pressure by turning every workflow into a potential source of dynamic, machine-speed access requests. Static roles, standing privileges, and ticket-driven approvals were never designed for that world.
Agents are a new identity type
To work safely at enterprise scale, agents cannot be treated as shadow users, generic service accounts, or invisible extensions of human credentials. They need to be governed as first-class identities.
That means recognizing what makes them fundamentally different from humans. Humans work in bursts. Agents run continuously. Humans can tolerate friction and delay. Agents are designed to operate in real time. Human access patterns are relatively bounded and explainable. Agent activity is dynamic, adaptive, and high-volume by design.
A modern access model has to account for all of that. It has to understand who the agent is, who it is acting for, what it is trying to do, what data it needs, and how long that access should last. It also has to make those decisions quickly, consistently, and with a clear audit trail.
What Immuta is launching
Immuta’s Agentic Data Access capabilities are built for exactly this moment.
With Agentic Data Access, Immuta treats AI agents as first-class participants in the data ecosystem. Rather than borrowing a user’s identity, the agent has its own identity, attributes, intent, and audit trail. When an agent needs data, Immuta evaluates the request in context: who is acting, who the agent is acting for, what data is being requested, and why it is needed.
Based on centrally defined policies, Immuta then provisions temporary access directly in the underlying data platform—such as Snowflake, Databricks, or BigQuery—granting only the access required for that task and automatically removing it when the task is complete.
This is a fundamentally different model than pushing authorization decisions up into the LLM tier and hoping for the best. Immuta enforces deterministically at the data platform tier, where governance has to be real, provable, auditable, and fast enough to keep up with machine-speed workflows.
What this enables
- Agents act on behalf of users, not as users.
- Access is just in time, least privilege, and ephemeral.
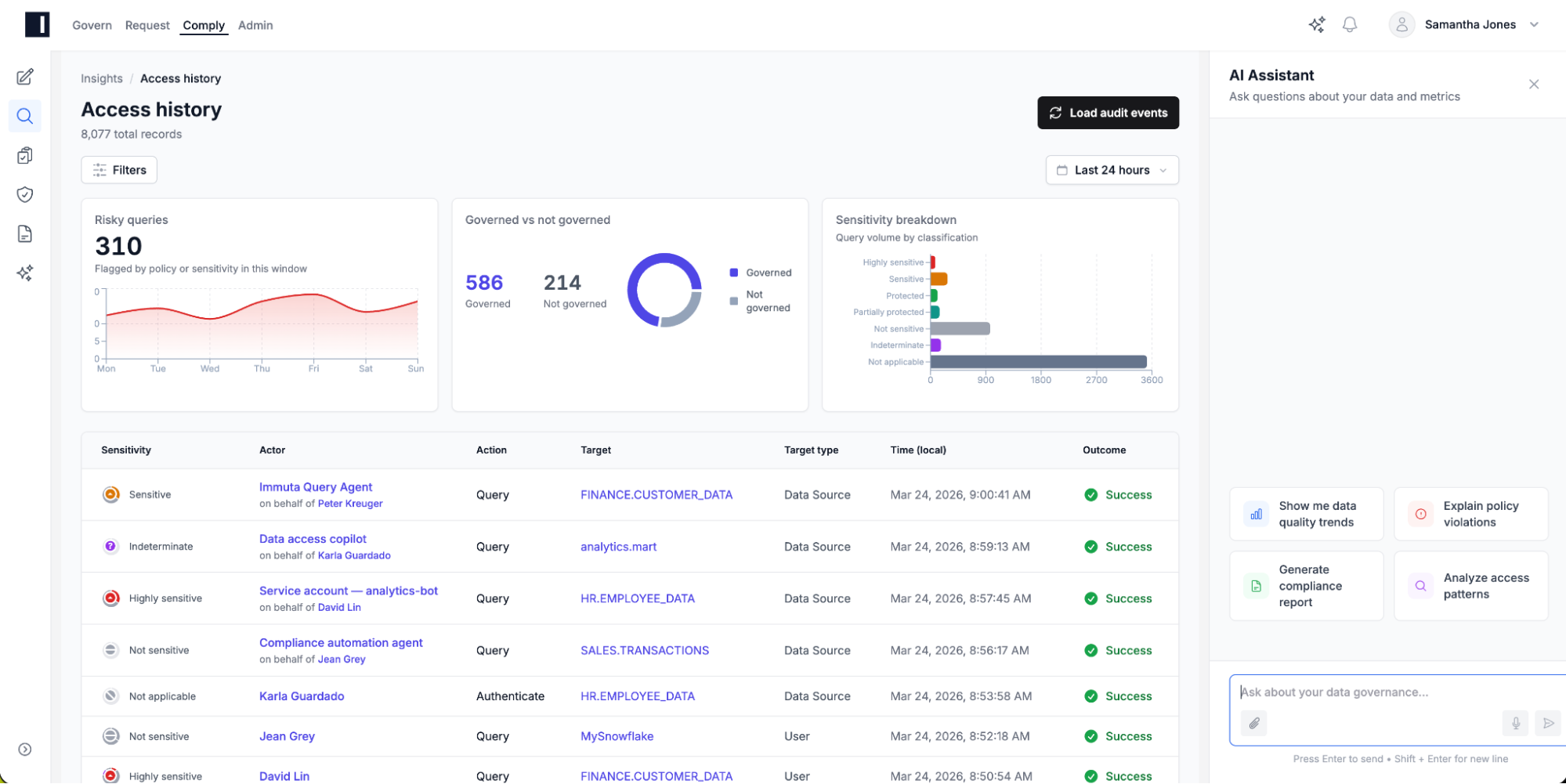
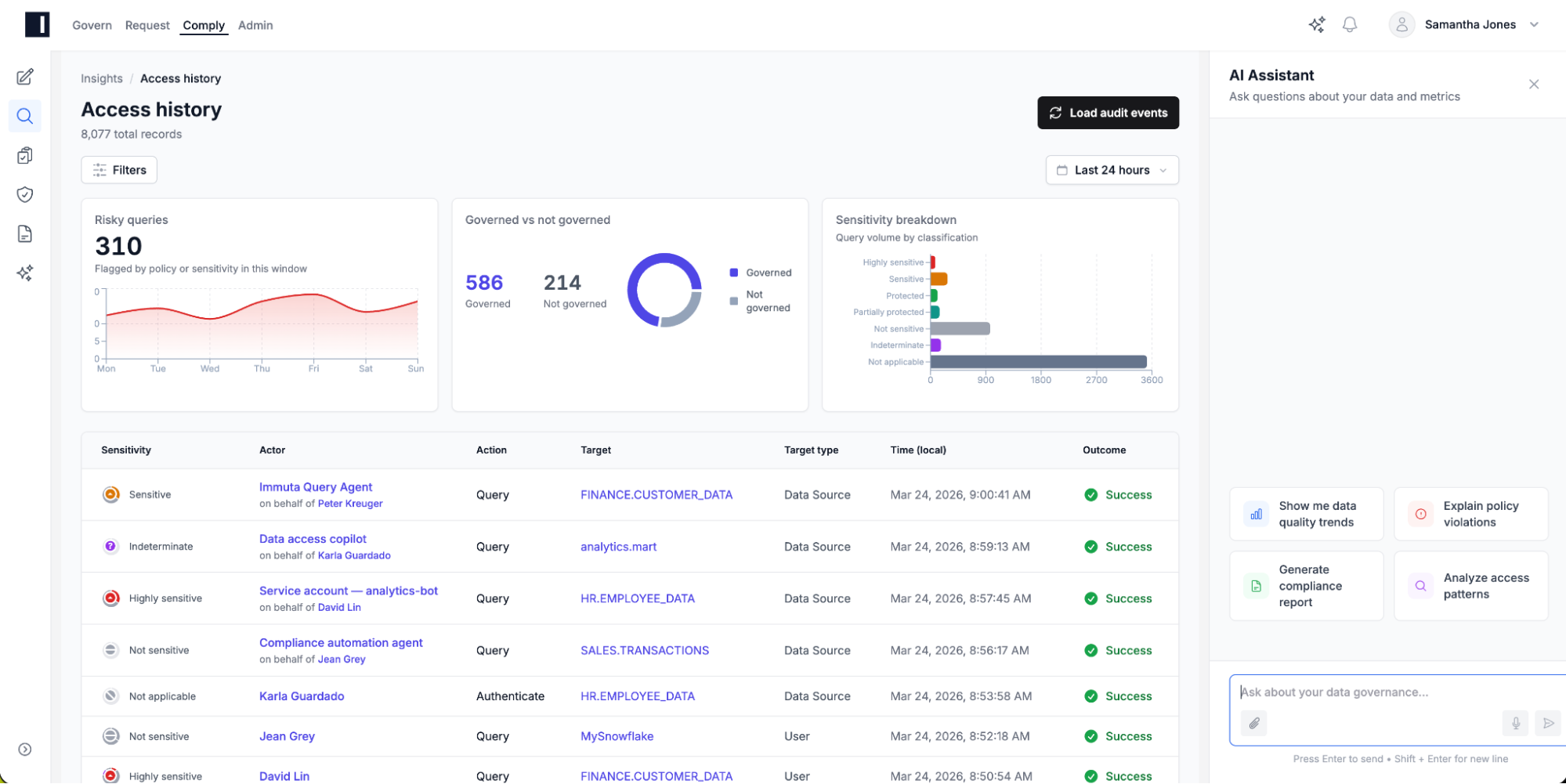
- Every action is traceable across the human, the agent, the purpose, and the data accessed.
- Enterprises reduce account sprawl, eliminate standing privileges, and preserve accountability.
Why Immuta is uniquely positioned
What makes this announcement powerful is not just the product capability. It is the architecture, operating history, and customer proof behind it.
This is not Immuta trying to bolt AI language onto a legacy access model. It is the natural extension of the platform we have been building from the beginning. Since the cloud era took hold in 2018, we have been building an abstract and decoupled policy management layer into cloud data infrastructure so governance teams can author policy once and enforce it natively across a complex data ecosystem.
That architectural choice matters now more than ever. Agentic access cannot be governed reliably from a layer that sits above the data and guesses. Policy has to perform in real time, provision access just in time, and leave behind a clear audit trail in the underlying data platforms where enterprise governance actually lives.
That is why, in our view, no company is better positioned to perform and scale policy for the agentic era. Many companies talk about policy. Very few have proven they can author it once, enforce it natively, and operate it across the scale, complexity, and regulatory demands of the world’s largest enterprises.
Immuta does this with some of the biggest and most complex organizations in the world, including J.P. Morgan, Booking.com, Cigna, Roche, General Motors, and many more. These are enterprises with global operations, sensitive data, strict compliance requirements, and high expectations for performance. If a policy model can hold up there, it can hold up in a world where agents are making requests continuously, across systems, at machine speed.
You can think of Immuta’s evolution in three eras. Era 1 was data security: separate policy from platform, author once, and enforce fine-grained access natively across a complex data ecosystem. Era 2 was data provisioning: move beyond static entitlements and manual tickets to a workflow-driven model where access can be requested, reviewed, approved, potentially automatically through deterministic rules, and provisioned quickly and safely. Era 3 is agentic governance: govern access for a world where the fastest-growing class of data consumer is non-human.
It may feel like the market jumped from Era 1 to Era 3 overnight. But Era 2 is exactly what makes Era 3 possible. You cannot safely support agentic access without policy externalization, native enforcement, approval routing, just-in-time provisioning, and unified auditing already in place.
The market compressed those eras faster than anyone expected. What looked like a future roadmap started arriving all at once. But the reason Immuta can meet this moment is that we already built the core pieces, and we built them into the cloud data stack where governance has to happen. That is why this is not a pivot. It is a continuation. We have been building toward a world of dynamic, policy-based, real-time access for years. AI agents simply made the need urgent.
Where this goes next
Agentic Data Access is the foundation, not the finish line.
The next step is helping agents understand not just whether they can access data, but how to use the right data safely and efficiently. That is where semantic governance comes in: extending access awareness into the semantic layer so agents can understand which metrics, fields, and relationships a user is allowed to use before they ever generate a query.
After that comes question-time approval: the ability for agents to request additional access on behalf of users in real time, with deterministic policy automation for straightforward cases and human review for exceptions.
Together, those capabilities move the industry beyond access control and into access orchestration—where agents can safely discover, request, and use data in a governed, auditable, machine-speed workflow.
A new era of data access
We are entering a world where more access requests will come from agents than from people.
The organizations that win in that world will not be the ones that simply open the floodgates or lock everything down. They will be the ones that can provision the right access for the right task at the right time, with governance, accountability, and speed built in.
That is the future Immuta is building. And while the moment arrived faster than we expected, the direction did not surprise us at all.