Structure-first controls for clinical trial data, real-world data, and other sensitive regulated datasets.
Introduction
Immuta does not make a pharmaceutical company GxP compliant by itself. What it does exceptionally well is strengthen the technical control environment required for a GxP-ready data estate: it makes sensitive data easier to identify, policies easier to author and revoke, eligibility rules easier to enforce, and audit evidence easier to unify across major data platforms.
That matters because GxP inspections and internal quality reviews repeatedly come back to the same questions: who had access, to what, when, where, why, how, and under which controls. Immuta helps a pharma organization answer those questions with far more consistency and far less manual effort.
| Audience | Use case focus | Prepared |
|---|---|---|
| Data, security, platform, QA, and compliance leaders | Clinical, RWD/RWE, PHI/PII, collaborative analytics | March 25, 2026 |
Executive summary
Pharmaceutical companies are trying to run regulated processes on top of data estates that are no longer centralized, homogeneous, or easy to inspect. Clinical trial data, real-world data, safety data, manufacturing data, and collaborative analytics increasingly span Snowflake, Databricks, BigQuery, Redshift, Trino, PostgreSQL, SQL Server, Teradata, and adjacent catalog or identity systems. The core GxP expectations, however, have not become simpler: regulated firms still need trustworthy records, role-appropriate access, risk-based controls, inspection-ready evidence, and the ability to show that access decisions are controlled rather than ad hoc.
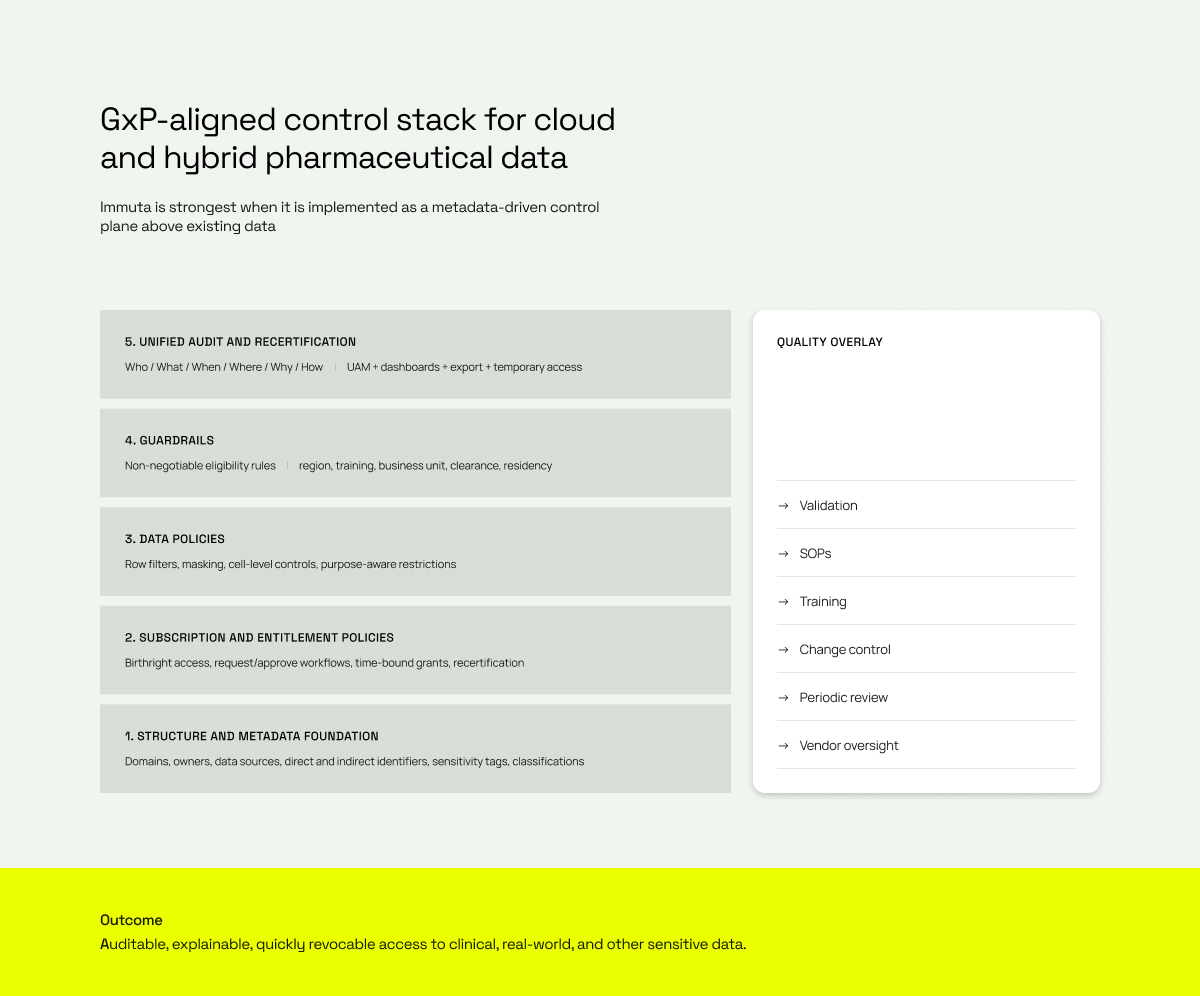
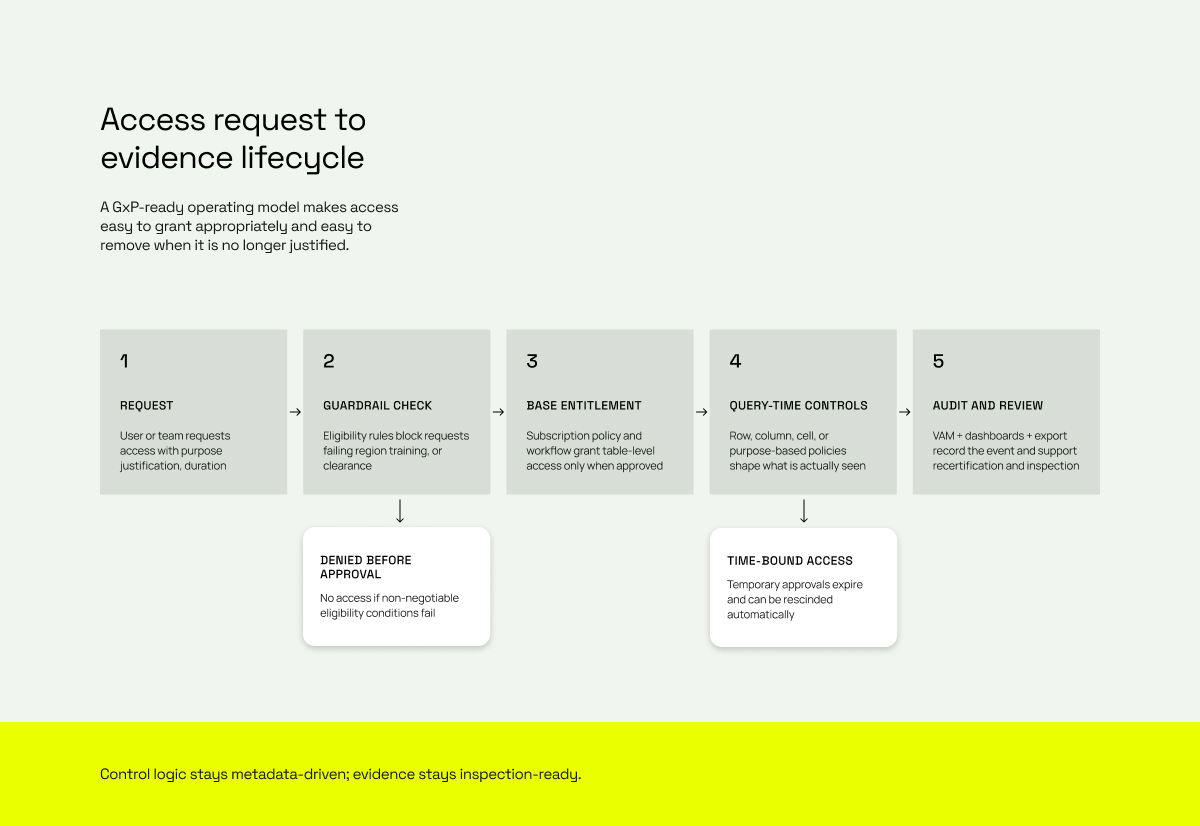
Immuta is valuable in this context because it functions as a metadata-driven policy and evidence layer over existing data platforms. Instead of forcing each platform, project, and steward to solve access control independently, it gives pharma organizations a way to build a more coherent control stack around five disciplines: (1) structure and classification, (2) policy authoring plus governed request and masking-exception workflows, (3) guardrails and residency controls, (4) unified audit and recertification, and (5) accountable human-and-agent access for emerging AI-driven use cases.
Bottom line
- A structure-first approach matters. If a dataset is not consistently identified, classified, owned, and tagged, it will not be consistently governed or auditable.
- Immuta helps organizations move from platform-specific permissions and ticket queues to policy-based access with explainable evidence.
- Guardrails matter because some access conditions should be non-negotiable: geography, training, role, business unit, approved project, or study-team membership.
- Unified audit matters because GxP reviews rarely ask only whether a policy exists. They ask whether the policy was actually in force when a user queried a regulated dataset.
What this paper assumes
This white paper is written for life sciences organizations evaluating how Immuta can materially improve the access-control, data-governance, and auditability layers of a pharmaceutical data environment. It deliberately avoids claiming that software alone creates compliance. GxP compliance still requires a fit-for-purpose operating model including intended-use definition, vendor qualification, validation, SOPs, training, change control, periodic review, and quality oversight.
In this paper, GxP means more than one domain
The control patterns described here are most directly relevant to GCP, GMP, GLP, pharmacovigilance, and adjacent regulated data handling scenarios. The same technical capabilities also support overlapping privacy and data-protection obligations such as HIPAA and jurisdiction-specific residency rules, especially when clinical and real-world datasets contain direct or indirect identifiers.
1. Why pharmaceutical companies need a structure-first governance model
In regulated environments, access governance fails long before policy syntax fails. It fails when the organization cannot reliably answer simple structural questions: What is this dataset? Who owns it? Which identifiers does it contain? Is it direct identifier data, indirect identifier data, or de-identified-but-reidentifiable when joined? Which studies, geographies, or business domains does it belong to?
For pharmaceutical companies, those questions are especially important because modern data programs increasingly combine internal trial data, external data feeds, EHR-linked data, biomarker data, and commercial or manufacturing analytics. A single policy mistake can expose the wrong subject cohort, create cross-border access issues, or leave an organization unable to explain whether masking and restriction logic was applied consistently.
Questions QA, privacy, and inspectors routinely ask
- Who had access to Study ABC123 or a particular clinical dataset during a defined period?
- Which users accessed direct identifiers, and which only saw masked or filtered data?
- Was access granted because of birthright rules, a manual exception, or a time-bound approval?
- Which controls were in force when the query ran: row filter, mask, purpose restriction, or guardrail?
- Did the user remain eligible based on training, geography, project membership, or role?
- Can the organization reconstruct the evidence trail without manually reconciling logs from several platforms?
Structure is the prerequisite for auditable control
The central idea is simple: you cannot govern or audit what you cannot consistently classify. Structure comes first. In an Immuta program, structure means registered data sources, explicit ownership, governance domains, standardized metadata, automated identification of sensitive fields, context-aware classification, and tags that can be reused in policies and dashboards. Once that foundation exists, the rest of the control model becomes far more reliable and scalable.
2. How Immuta strengthens the GxP control environment
2.1 Data discovery, identifiers, and sensitivity classification
Immuta’s discovery model is particularly useful for pharma because it separates identification from classification. Identification determines what a column appears to be based on patterns and configured rules. Classification then adds contextual meaning and risk level based on how those fields appear together and how the organization wants to interpret them. That is exactly the difference between finding a date-of-birth field and recognizing that a table becomes sensitive when date of birth, site, rare disease, and subject attributes appear together.
This maps well to the pharmaceutical need to distinguish direct identifiers from indirect identifiers and to apply governance based on the real re-identification risk of the dataset, not only the label of an individual column. The result is a more defensible way to show why a dataset received a certain sensitivity class and why a particular access policy automatically attached to it.
Immuta also allows the company to push this structure into repeatable operating units: domains, owners, tags, and policy targets. That means new tables do not have to start from scratch every time. If the metadata is good, new data can inherit the right control intent rather than relying on a person to remember each rule manually.
Why this matters for GxP
- It becomes easier to prove that regulated data was identified intentionally, rather than discovered accidentally during an audit.
- Sensitive-data policies can attach to classes of data instead of depending on manual one-offs.
- Audit dashboards become more meaningful because access events can be viewed through the lens of sensitivity and classification.
- The operating model becomes more resilient to change: new columns, new tables, or new data products are less likely to escape governance.
2.2 Policy authoring, governed requests, and fast revocation
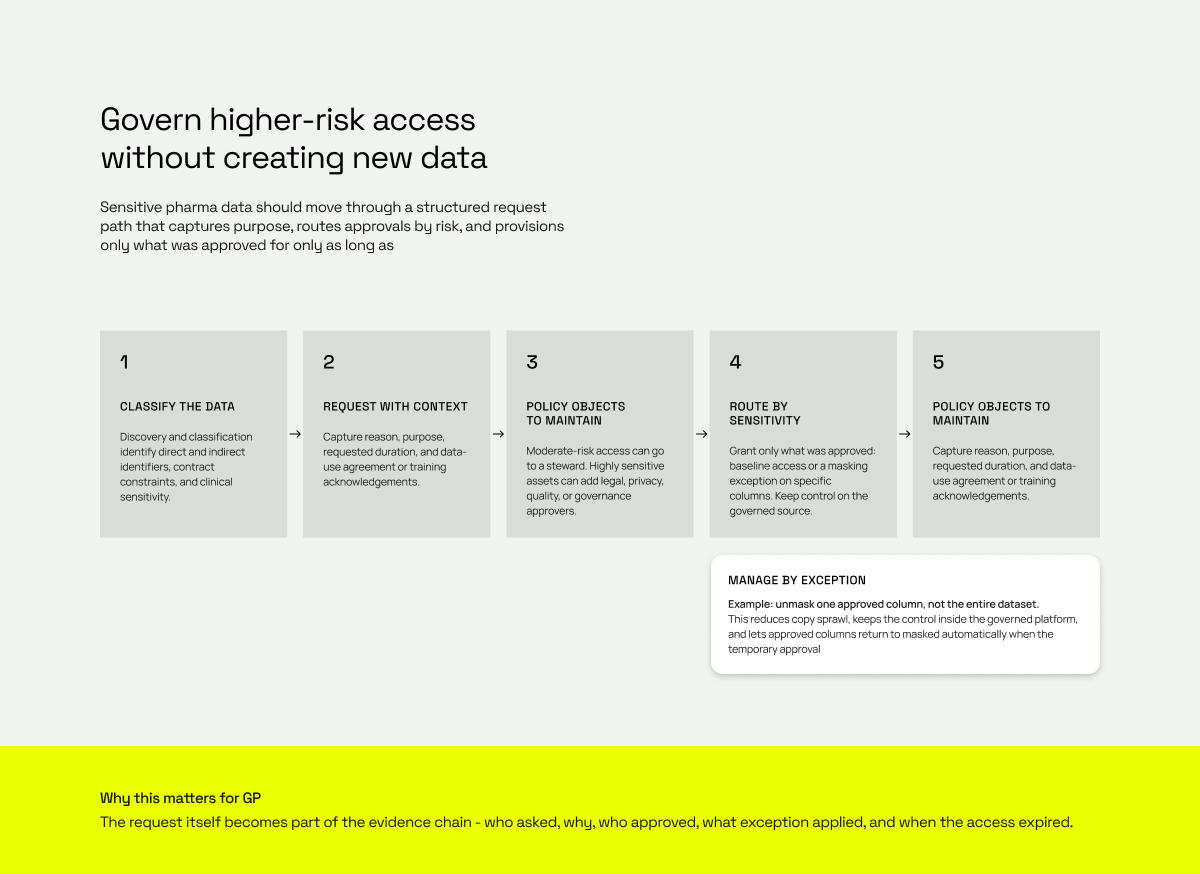
From a GxP perspective, the question is not merely whether a user could open a table. The question is whether the organization can demonstrate that access was appropriate, minimal, and revocable. Immuta helps by separating the access problem into at least two levels: subscription policies that govern whether someone may access a data source at all, and data policies that govern what they actually see once they query it.
This is precisely where a pharmaceutical company can build a cleaner model than “grant everyone who asks.” Subscription policies are well-suited to birthright or baseline access driven by attributes such as function, team, business unit, geography, or approved program membership. Sensitive-data policies then add the second layer: row filtering, column masking, cell-level rules, time-based restrictions, and purpose-based exceptions. In other words, a user may be allowed near the dataset without necessarily being allowed to see every value inside it.
For clinical and real-world datasets, that distinction is powerful. It supports operating patterns such as default masked access, with unmasked access available only when the user is acting under an approved purpose, belongs to the right study team, or has received a time-bound exception. That is usually much closer to least privilege than static, broad platform roles.
A critical extension of this model is the request layer. In a pharmaceutical company, not every request should follow the same path. A moderately sensitive dataset may require steward review only, while highly sensitive clinical, real-world, PHI, or contract-bound data may require additional legal, privacy, quality, or corporate-governance approval. Immuta’s request workflows make that operating model more explicit: request forms can capture reason, purpose, duration, and agreement acknowledgements, and review flow can be driven by the sensitivity or governance context of the asset.
Just as important, users can request policy exceptions instead of broad new extracts. A common pharma example is a masking exception on one or more approved columns. Rather than copying a dataset to create a second, less-governed version, the organization can temporarily unmask only the fields needed for the approved person and use case while the rest of the policy stays in force. That reduces copy sprawl, shrinks surface area for leakage, and keeps the control logic inside the governed platform.
Because both access approvals and masking exceptions can be time-bound, the request layer becomes part of continuous recertification. Access can auto-expire, approved columns can return to masked state automatically, and users can re-request only what they still need. For GxP, this creates a cleaner evidence chain: what was requested, by whom, for what purpose, who approved it, what policy or exception was applied, and when it expired.
Policy design principles that fit regulated pharma environments
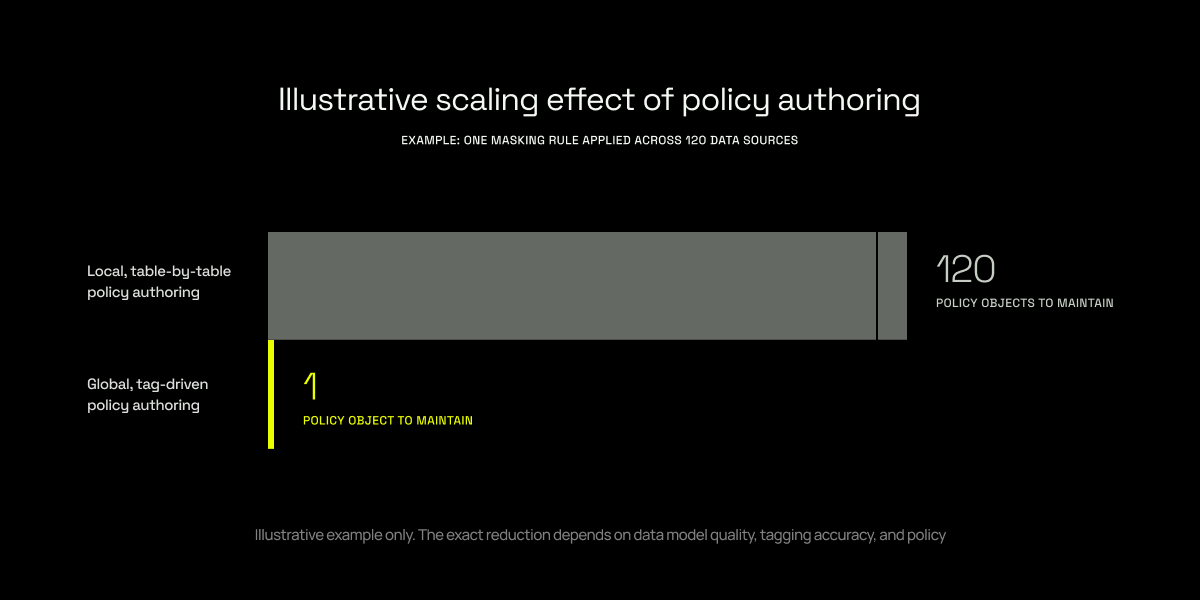
- Author global tag-based policies wherever possible so one rule can scale across many data sources.
- Use birthright access only for data that truly should be routinely available to a role or user segment.
- Route higher-risk requests according to classification, contractual obligations, and separation-of-duties needs; highly sensitive data may require steward plus privacy, legal, quality, or governance review.
- Prefer managing by exception – for example, temporarily unmasking one approved column – instead of generating derivative copies of regulated data.
- Design for rapid revocation: temporary approvals, expiration, and recertification should remove access as quickly as it was granted.
- Prefer policies referencing user metadata, groups, and purposes rather than individual named users. That is more scalable, less error-prone, and easier to defend during review.
A practical pharma pattern
- Use subscription policies to determine who may access or request a trial, program, or domain at all.
- Use request forms to capture reason, purpose, duration, and any data use agreement for sensitive access.
- Route high-sensitivity or contract-bound data to stewards plus legal, privacy, quality, or governance reviewers when needed.
- Use masking exception requests to unmask only approved columns temporarily instead of issuing new copies.
- Set duration on higher-risk approvals so access and unmasking are removed automatically unless actively renewed.
2.3 Guardrails and residency: preventing the “wrong approval” problem
Many access programs fail not because approvers are careless, but because the approval model is missing hard boundaries. In a GxP environment, some conditions should not be negotiable. A user may need to sit in the right legal entity or geography. They may need a specific training record, role clearance, project assignment, or research function. Even if someone mistakenly approves a request, the system should still block access if those baseline conditions are not met.
This is where guardrail policies are especially compelling. Guardrails act before the approval decision is finalized. They create the pool of people who are even eligible to request a dataset. That is a strong fit for residency zones, country restrictions, “confidential clinical research” classifications, CRO versus internal access separation, and any scenario where trial data should remain tightly bounded by role and jurisdiction.
The dynamic aspect matters too. If the user’s metadata changes—for example, a required training expires, a project assignment ends, or the person transfers out of a region—the eligibility state can change with it. This is materially different from static role grants that linger after the original business need has disappeared.
Examples of guardrail rules that resonate in pharmaceuticals
- Only users in approved countries or residency zones may request data containing trial-subject level information.
- Only users with current GxP, privacy, or clinical-research training may request certain classifications of data.
- Only members of a specific study team, therapeutic area, or clinical operations group are eligible for access.
- Only personnel with the right business function and clearance may access confidential R&D or patient-level data.
3. Unified audit, recertification, and inspection readiness
The compliance value of controls rises sharply when the organization can reconstruct evidence quickly. That is why unified audit is not a reporting convenience; it is part of the control model itself. Immuta’s audit capability normalizes supported events such as query activity, authentication, policy changes, access approvals, exceptions, project activity, and tag events into a common structure. When classification is enabled, dashboards can also reflect the sensitivity of the data being accessed.
Operationally, this means teams can investigate from multiple entry points. They can start from a clinical trial or schema, a data product, a specific user, an application or service principal, a date range, a policy, an exception, or a sensitivity class. They can then work across the same evidence fabric instead of stitching together logs from each platform by hand. For prospects who care about “Who got access to what, when, where, why, and how?”, this is one of the strongest parts of the Immuta story.
Just as important, Immuta can support continuous recertification rather than periodic spreadsheet cleanup alone. Temporary access can expire. Migration to Immuta can be used as a one-time entitlement reset. Exceptions can be re-requested with justification. This lowers the risk of stale permissions and makes the evidence trail for retained access much clearer.
Separate but related, agentic access extends the same evidence model to non-human actors. As AI agents begin consuming regulated data, the company should be able to attribute activity to the right agent, the right sponsor, and the approved purpose without redefining unified audit as an AI-only capability.
What a strong audit model allows a pharma team to do
- Show which users, applications, or service accounts touched a regulated dataset and whether access was baseline, temporary, or exceptional.
- Show which controls were relevant at the time: subscription policy, mask, filter, purpose, exception, guardrail state, or expiration window.
- Trace the relationship between the original request, reviewer decision, applied entitlement, and the actual access event.
- Show sensitivity-aware activity when discovery and classification are in place.
- Export audit data to an enterprise retention store so evidence remains available for long-term review.
- Drive recertification from actual access patterns instead of assumptions about who still needs a role.
Important implementation note
- Audit depth and policy support vary by integration. Immuta normalizes supported events across platforms, but not every platform yields the same level of detail for rows returned, columns returned, or unauthorized access signals.
- For GxP programs, plan the evidence architecture intentionally: define which platforms are in scope, which audit fields are needed, and how long logs must be retained outside the default operational window.
4. Mapping Immuta capabilities to common GxP control objectives
The following alignment matrix is intended to support executive and technical evaluation. It is not legal advice and it is not a substitute for validation or a formal quality assessment. It shows where Immuta is a strong technical enabler, what evidence it can help produce, and what still remains the responsibility of the regulated company.
| Control objective (and common anchor) | How Immuta contributes | Evidence or operational output | Still required from the pharma organization |
|---|---|---|---|
|
Identify data requiring control Part 11 / Annex 11 / MHRA data integrity |
Registers data sources, owners, domains, identifiers, and contextual sensitivity classes so policy can attach to the right data automatically. | Tags, classifications, domain ownership, sensitivity-aware dashboards, policy targets. | Steward review, taxonomy design, validation of intended use, source-data standards. |
|
Restrict access to authorized personnel Part 11 / Annex 11 personnel and access expectations |
Uses subscription policies, attributes, groups, and governed request workflows - including sensitivity-based routing - to govern table-level access and baseline entitlements. | Approved access requests, reviewer decisions, applied subscription rules, masking exception history, temporary approvals. | Role design, HR/identity quality, SOPs for request and approval authority. |
|
Apply least privilege within datasets Risk-based data exposure control |
Uses row-level, column, cell, time-based, and purpose-aware data policies so users do not automatically see every value in an approved table. | Masking rules, row filters, policy states, policy activity events, query results shaped by policy. | Policy standards, business rule review, validation of the configured control logic. |
|
Prevent access that should never be allowed Residency, role, training, or legal boundary controls |
Uses guardrail policies to define non-negotiable eligibility before approval can succeed. | Eligibility logic, denied or blocked requests, dynamic alignment to metadata changes. | Definition of hard boundaries, authoritative upstream attributes, governance sign-off. |
| Control objective (and common anchor) | How Immuta contributes | Evidence or operational output | Still required from the pharma organization |
|---|---|---|---|
|
Maintain attributable, reviewable access evidence Part 11 auditability / Annex 11 lifecycle risk management |
Normalizes supported events across query, authentication, policy, access approval, exception, project, and tag activity, and supports sensitivity-aware dashboards. | Unified audit records, dashboards, exported logs, searchable request history, and query activity. | Retention schedule, enterprise archive, evidence review procedure, investigation playbooks. |
|
Control access changes and policy changes Change control and inspection readiness |
Supports policy states, activity history, and auditable policy events for global and local policy changes. | Policy-created, updated, removed, conflict-resolved, and applied event history. | Formal change control, validation evidence, release governance, approval records. |
|
Remove stale entitlements quickly Periodic review / recertification |
Supports temporary approvals, expiration, request-and-approve workflows, and one-time or ongoing recertification patterns. | Expiration records, renewed requests, cleaner entitlement baseline, reviewable exception history. | Access review cadence, attestation ownership, escalation process, exception policy. |
|
Support inspection and forensic questioning Who / what / when / where / why / how |
Provides a unified lens to investigate by user, agent, dataset, schema, table, policy, purpose, sensitivity, or time window. | Reconstructable evidence for human and agent access decisions and query behavior across supported platforms. | Inspection narratives, cross-system correlation, source-record governance, CAPA process where needed. |
5. Where Immuta is especially strong for pharmaceutical use cases
| Use case | Control pattern that matters most | Why pharma teams care |
|---|---|---|
| Clinical trial data | Guardrails + masked defaults + study/team-based exceptions | Keeps subject-level data inside approved teams and regions while still enabling analysis. |
| Real-world data / RWE | Direct and indirect identifier classification + purpose-based access | Reduces the risk of overexposure in linked datasets where re-identification risk is contextual. |
| Cross-functional R&D analytics | Birthright access for low-risk data + request workflow for sensitive data | Birthright access for low-risk data + request workflow for sensitive data |
| Data marketplace / data mesh | Global policies targeted by tags and domains | Lets domains publish data products without each team reinventing policy logic. |
| External collaborators / CROs | Residency and role guardrails + temporary approvals | Makes collaboration easier to justify, easier to expire, and easier to inspect. |
| AI agents and advanced analytics | Separate agent identity + approved purpose + question-time approval + unified audit | Separate agent identity + approved purpose + question-time approval + unified audit |
6. What Immuta does not replace
Immuta is a strong platform for data access control, metadata-driven governance, and unified audit. It is not the entire GxP system. It should be positioned as a high-value control layer within a broader validated operating model.
Immuta does not replace these obligations
- Computer system validation or risk-based validation of the implemented configuration for intended use.
- SOPs and quality governance for approving, reviewing, and changing access-control logic.
- Source-system controls for original GxP record creation, e-signatures, archival, and record retention where those functions live elsewhere.
- Upstream identity quality in systems such as Okta, Azure AD, LMS tools, HR systems, or project master data.
- Security architecture basics such as network, encryption, backup, incident response, and platform hardening.
7. A practical implementation blueprint for a pharma program
A pharmaceutical deployment is strongest when it is staged deliberately. The point is not to turn on every feature at once; it is to build an evidence chain that improves with each phase.
| Phase | Focus | Core configuration outputs | Quality / evidence outputs |
|---|---|---|---|
| 1 | Intended use and scope | Identify in-scope platforms, regulated data domains, user populations, and evidence needs. | URS/risk assessment inputs, validation strategy, control objectives. |
| 2 | Structure foundation | Register data sources, assign ownership, create domains, configure identifiers and classification frameworks. | Metadata standards, ownership model, sensitivity taxonomy. |
| 3 | Baseline entitlements | Define birthright access and subscription policies for common low-risk access patterns. | Access model documentation, approval roles, exception process. |
| 4 | Sensitive data controls | Implement row, column, cell, time, and purpose-aware policies for PHI, PII, and trial-sensitive data. | Policy test cases, expected-results evidence, review sign-off. |
| 5 | Guardrails and residency | Add eligibility rules for geography, training, project membership, business unit, or legal boundary. | Hard-boundary evidence, escalation workflow, governance approvals. |
| 6 | Unified audit, recertification, and agentic oversight | Enable dashboards, exports, retention, temporary approvals, recurring access review, and separate human-versus-agent audit semantics for approved AI use cases. | Inspection narratives, retained audit evidence, recertification metrics, approved agent inventory. |
A rollout principle worth emphasizing
Do not start with hundreds of local exceptions. Start with a clean policy backbone: data structure, birthright access, core sensitive-data controls, and a deliberate recertification event. Once that backbone is in place, higher-risk exceptions become easier to justify and easier to remove.
8. Conclusion
For a pharmaceutical prospect, the best Immuta story is not that it is another governance tool. The best story is that it helps turn a fragmented collection of permissions, tickets, native roles, and siloed logs into a structured, explainable, and inspectable access model. That matters directly to GxP because GxP does not reward the appearance of control; it rewards control that can be demonstrated.
When implemented well, Immuta helps a pharma organization do six things far better than a purely native, manual model: identify sensitive data earlier, route higher-risk access through governed requests, manage by exception instead of copying data, prevent inappropriate access before it is approved, reconstruct audit evidence faster across humans and agents, and revoke stale access more cleanly. Those are exactly the characteristics that make a modern pharmaceutical data environment more GxP-ready.
Selected product and regulatory references
The following public sources were used to ground the control statements in this white paper. Product capabilities should always be validated against the prospect’s target version, integration mix, and intended-use design.
| Organization | Reference | Link |
|---|---|---|
| Immuta | Driving Data & AI Innovation Across the Pharmaceutical Lifecycle | Open |
| Immuta | Healthcare & Life Sciences | Open |
| Immuta | Data Discovery & Classification | Open |
| Immuta Documentation | Data Identification | Open |
| Immuta Documentation | Data Classification | Open |
| Immuta Documentation | Authoring Policies at Scale | Open |
| Immuta Documentation | Subscription Policies | Open |
| Immuta Documentation | Data Policies Reference Guide | Open |
| Immuta Documentation | Implementing Guardrail Policies: A Strategic Guide | Open |
| Immuta Documentation | Universal Audit Model (UAM) | Open |
| Immuta Documentation | Audit Dashboards Reference Guide | Open |
| Immuta Documentation | The Value of Recertification When Migrating to Immuta | Open |
| Immuta | How Merck is Adapting Its Data Governance Strategy for AI & GxP | Open |
| Immuta | Roche is awarded IDC Best in Future of Intelligence award for implementing data mesh strategy at scale with Immuta | Open |
| FDA / eCFR | 21 CFR Part 11 - Electronic Records; Electronic Signatures | Open |
| FDA | Electronic Systems, Electronic Records, and Electronic Signatures in Clinical Investigations: Questions and Answers | Open |
| FDA | Data Integrity and Compliance With Drug CGMP: Questions and Answers | Open |
| European Commission | EU GMP Annex 11 - Computerised Systems | Open |
| ICH | E6(R3) Guideline for Good Clinical Practice | Open |
| MHRA | Guidance on GxP Data Integrity | Open |
| HHS | Summary of the HIPAA Security Rule | Open |
| Immuta Documentation | Manage Request Forms | Open |
| Immuta Documentation | Access to Data Products and Assets | Open |
| Immuta Documentation | Understanding Masking Exceptions and Underlying Policies | Open |
| Immuta | Simplifying Data Access with Multi-Approver Workflow | Open |
| Immuta | How AI Agents Change the Rules of Access Governance | Open |