The role-based access control versus attribute-based access control debate has been going on for decades. Now, as organizations move away from on-prem and Hadoop-era technologies in favor of modern, cloud-based data environments, the differences between the two security approaches are coming into sharper view. A new study from GigaOm comparing the two approaches head-to-head, using publicly available data, may finally put the debate to rest.
Why are more data teams considering ABAC? So they can maximize their cloud data investments. The flexible, scalable, dynamic nature of the cloud creates a highly heterogeneous environment — powerful for analytics, yet impractical without the right security and privacy controls. More data, more people, and more powerful compute engines, combined with more stringent security and privacy requirements, has created a perfect storm for data risk.
As access control models have evolved, attribute-based access control was conceived to be more automated and adaptive to the dynamic, ever-changing data environment that cloud data platforms enable. Even authorities like NIST have recommended attribute-based access control (ABAC) over role-based access control (RBAC) — and still, RBAC and its derivatives persist.
This puts data-driven organizations at a crossroads. Data teams can continue using the old standby, RBAC, which is mostly closely associated with Apache Ranger and worked well enough for Hadoop. Its enhancements, like role-based access control with object tagging (OT-RBAC), offer some degree of flexibility by enabling policy creation based on tags. But RBAC is inherently static and rigid. In today’s modern cloud environments, that won’t cut it.
So we’re in the midst of a paradigm shift from RBAC to ABAC. It’s similar to the one we’ve seen recently with the cloud. Prior to the cloud, organizations would have to decide on a software stack, procure servers to align with that stack, get everything running, then hope it succeeds. It’s a long process that locks you into static decisions made early on — there’s no scalability or evolvability. The shift to the cloud changed that, and the shift to ABAC is needed to align with the benefits of the cloud.
But what really is the benefit of ABAC, in terms of productivity, speed, and business value?
When we founded Immuta in 2015, we saw rapid growth in cloud adoption and knew it required a new, dynamic approach to data access control. To get ahead of these sweeping changes, we pioneered the first commercial implementation of ABAC, optimizing it for modern cloud environments. By separating policy from compute platform and making access decisions based on multiple dimensions at runtime, Immuta’s ABAC model matches the nature of the cloud: flexible, scalable, and dynamic. ABAC is built for the present, not the past.
With Immuta, our customers have been able to satisfy the same data security and access control requirements with far fewer policies, faster time-to-data, and apply dynamic, privacy-enhancing technologies (PETs) with ABAC. But how does that translate to scalability for your organization? And, how much does it impact the bottom line?
A new, independently conducted analysis by GigaOm may shed some light on these questions.
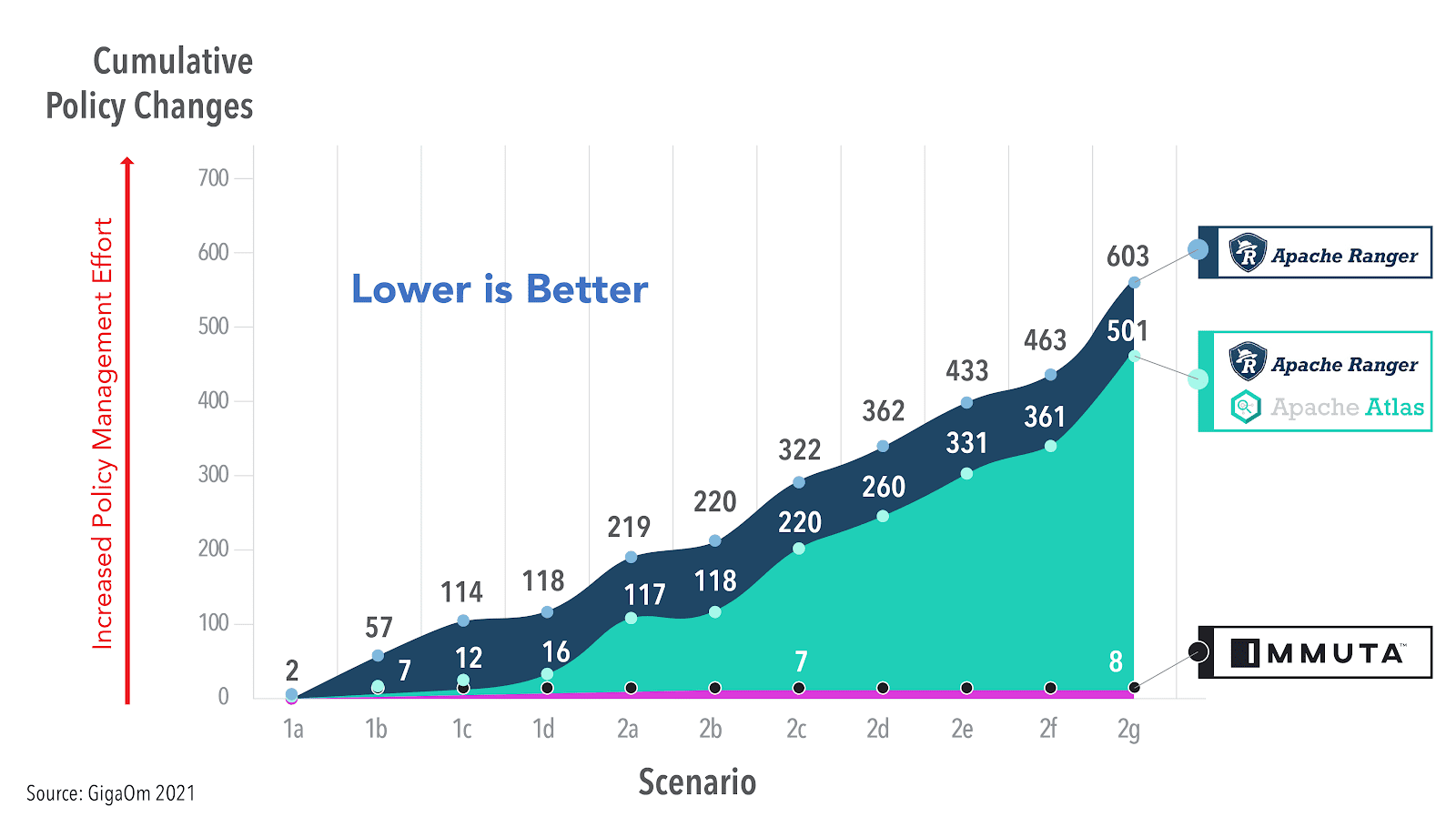
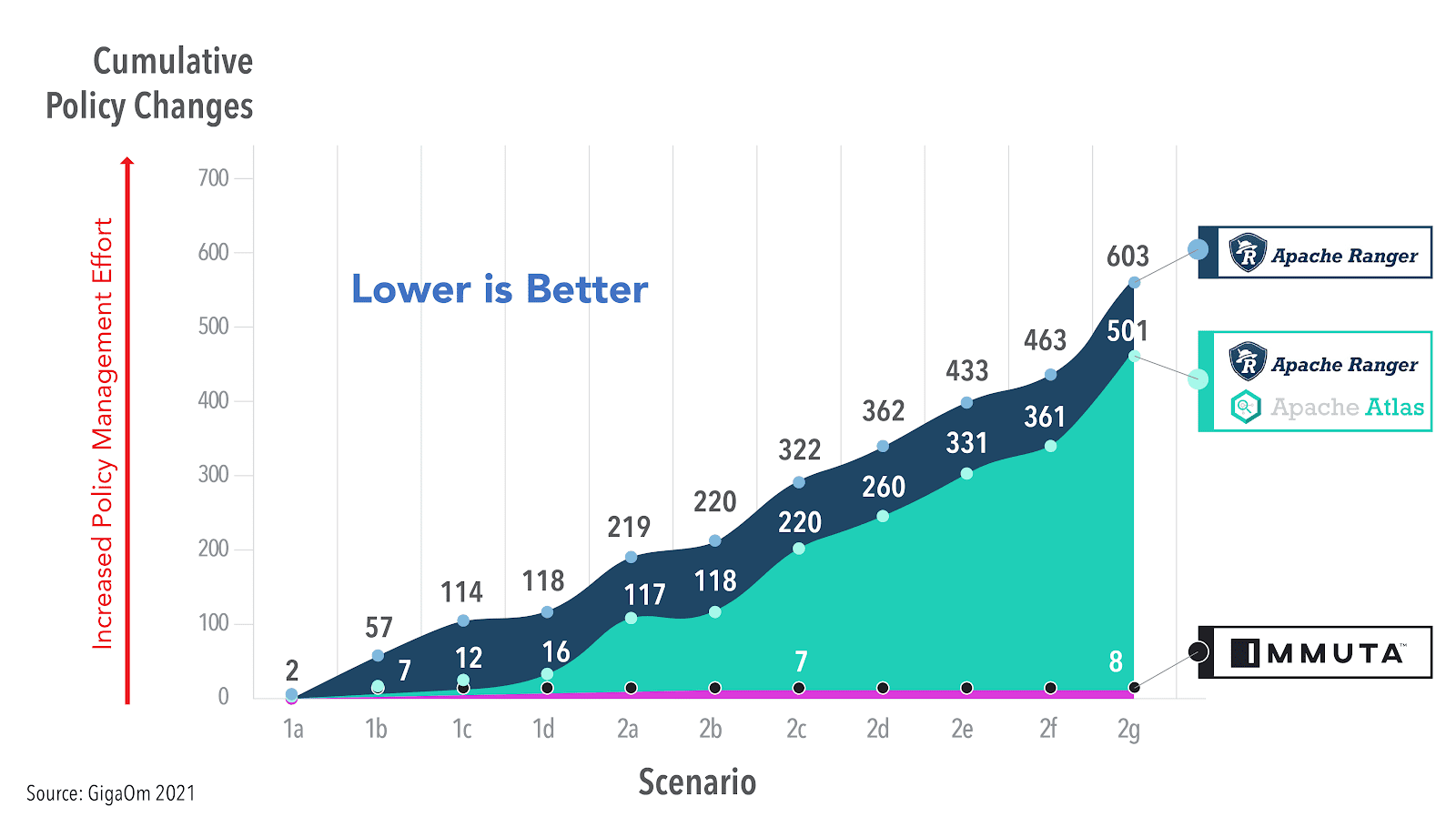
GigaOm pitted Ranger’s (+Atlas) OT-RBAC model against Immuta’s ABAC approach, and found that Ranger required 75x more policy changes than Immuta (603 policy changes vs. 8 policy changes total) to satisfy the same security requirements. Even when coupled with Apache Atlas for data discovery and tagging, Ranger still required 63x more policy changes than Immuta.
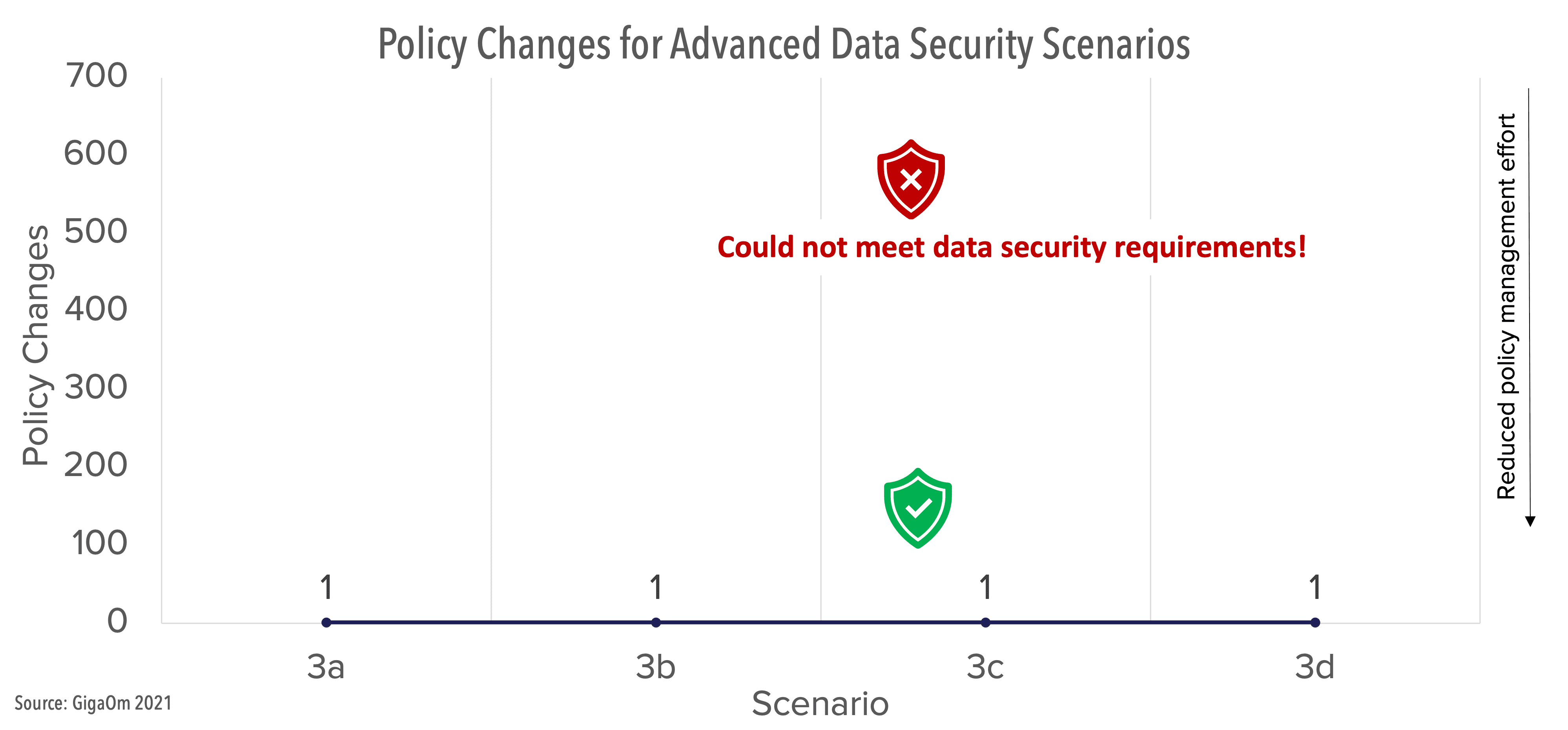
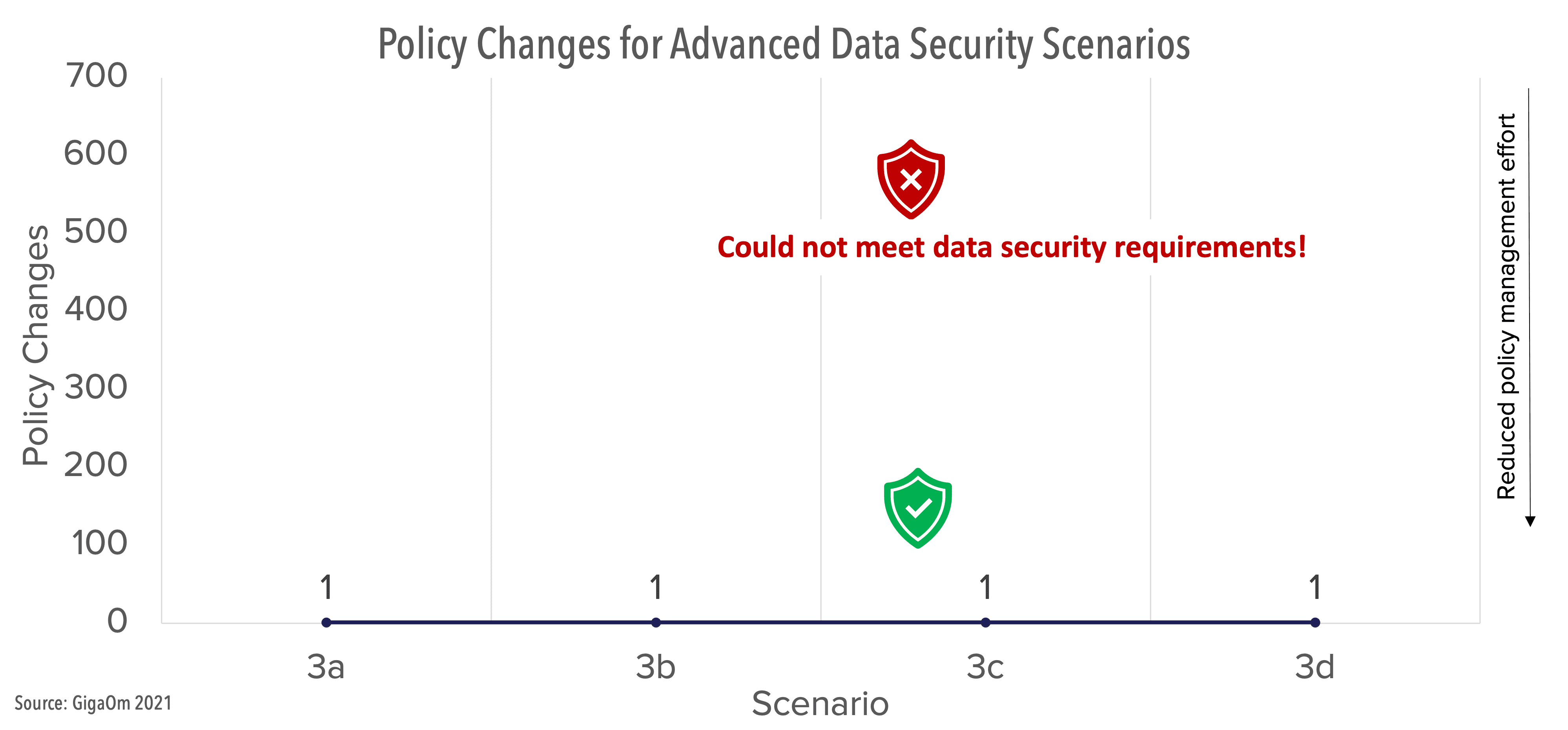
GigaOm’s team also tested OT-RBAC and ABAC on advanced access control capabilities. Ranger was unable to satisfy any of the data security requirements, while Immuta was able to meet each requirement with just a single policy change.
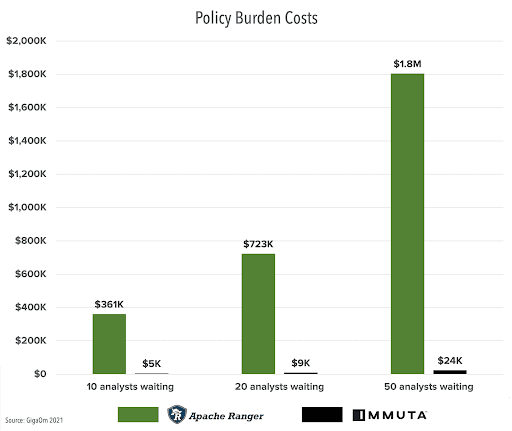
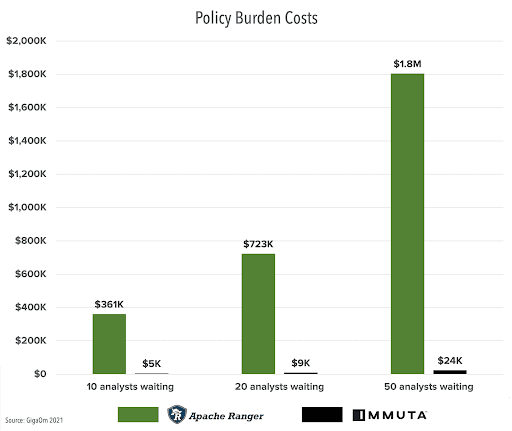
According to GigaOm’s (conservative) estimate, the downstream costs of using Ranger’s approach could equate to $300,000 in lost time and opportunity, versus less than $5,000 with Immuta — and this gap will widen as users, data sets, data platforms, or any number of variables increase. In short, role-based access control with Ranger will lose money and stifle ROI in cloud investments.
The case against OT-RBAC is no longer just hypothetical. Immuta’s unique ABAC approach delivers the efficiency, scalability, and bottom line results that data-driven organizations need to compete.