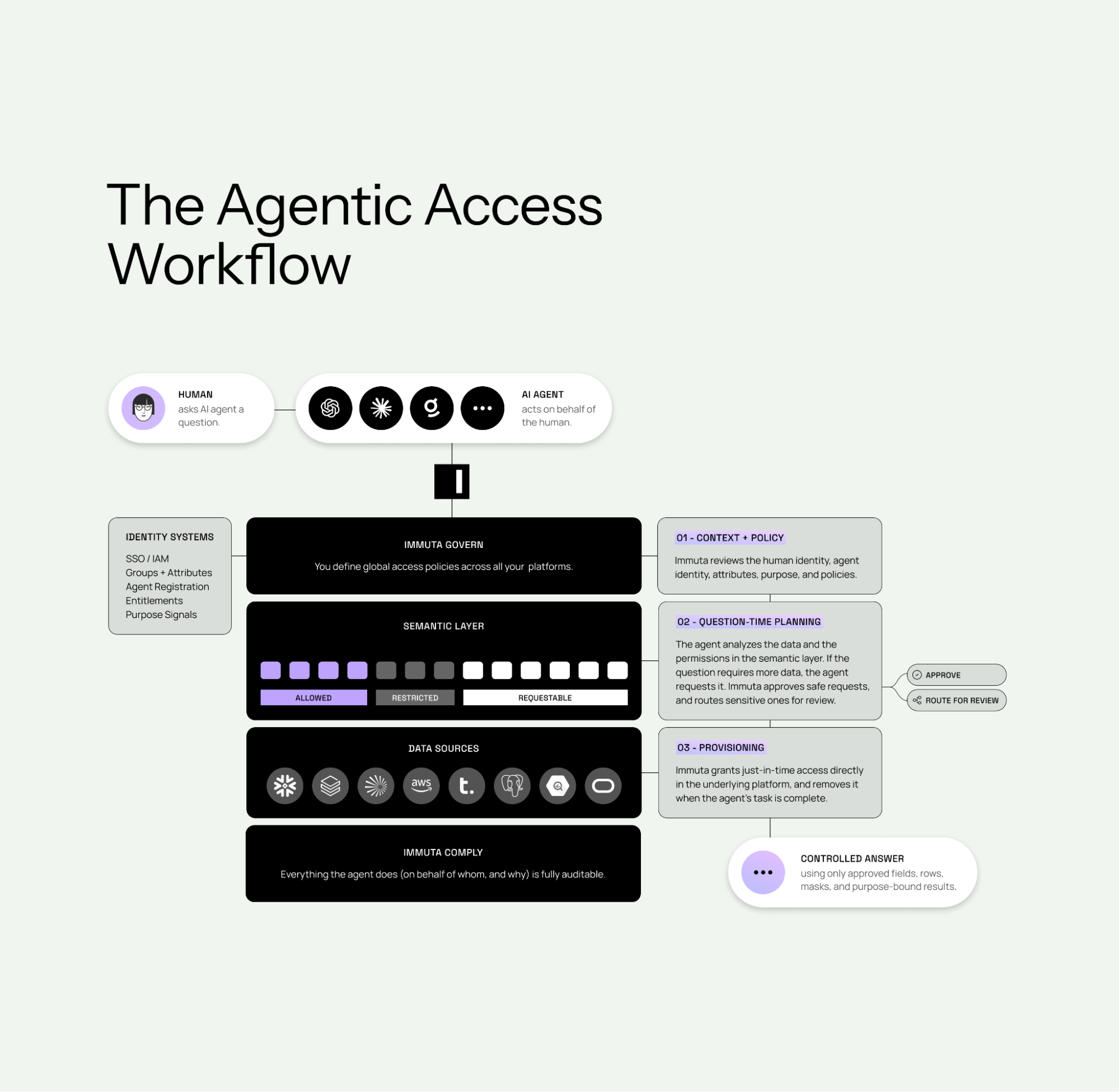
As Claude and other AI agents become a new interface to enterprise data, access governance becomes more important, not less. Organizations need to ensure agent-driven access is governed by policy, limited to the right context, and fully auditable across modern data platforms. With Agentic Data Access, Immuta extends its data provisioning platform to support AI agents as first-class data consumers, delivering governed access in real time.
AI agents do not operate within the limits of traditional human-scale access models. They move at machine speed, act continuously across systems, and increasingly operate on behalf of users. That creates a new enterprise challenge: how to make agent-driven access policy-driven, temporary, and auditable without falling back on static roles, impersonation, or ticket queues. Immuta addresses that challenge by extending data provisioning to support both human and non-human identities.
Watch the demo
Why AI agents need a different access model
In many early AI deployments, the simplest path has been to let the agent log in as the human asking the question. That may be enough for a pilot, but it does not work at enterprise scale. It creates the following problems:
- Account sprawl
- Expands standing exposure
- Increases the risk of rights inflation
- Makes it harder to maintain a clear audit trail.
It also limits the value of AI itself, because agents stall when they hit permission barriers or incomplete access context.
Traditional access workflows have a similar problem. They were built for occasional human requests, manual approvals, and ticket-driven processes. AI agents operate differently. They generate queries dynamically, move across systems continuously, and require access decisions in seconds, not days. That is why organizations need a different model for governing access in agent-driven workflows.
Governed access for agent-driven workflows
Immuta approaches this as an extension of data provisioning. The provisioning model spans three complementary patterns: Provision by Policy, Provision by Request, and Provision for Agents. That gives organizations one framework for predictable access, governed request workflows, and agent-driven access decisions.
Rather than forcing organizations into a separate access model, Immuta brings governed provisioning to the platforms they already use. That allows organizations to enforce policy directly where data lives, while continuing to use platforms like Snowflake, Databricks, and other modern data environments as their execution layer.
How Immuta vends roles for Claude
The first core mechanic is role vending. When an AI agent acts on behalf of a user, Immuta dynamically generates a temporary role in the underlying data platform that reflects only the permissions relevant to that specific task. That role is created at runtime and removed when the task completes.
That matters because it avoids the two most common bad alternatives: giving the agent the user’s full account permissions or relying on a broad static service account. Instead, each interaction is scoped to exactly what is needed and nothing more. The result is temporary, task-bound access rather than broad standing privilege.
In practical terms, this is how Claude can help answer a question over enterprise data without requiring broad standing access in the warehouse. Immuta provisions short-lived access directly in the data platform, aligned to the user context for that interaction and automatically removed when the task is done.
How Immuta policies control the data returned
Provisioning access is only half the story. The next question is what that access is actually allowed to reveal.
Immuta’s Data Policies define what a user sees once they have access, including table/view access, row filtering, column masking, and cell-level security. Those controls are enforced at query time, directly in the data platform, allowing the agent to interact directly with the data platform. Access to a table does not mean unrestricted access to every row or field inside it. An agent can return useful results while sensitive data remains masked until policy allows otherwise. The data platform’s native policies, administered by Immuta, dynamically shape query results based on who the user is, what the data contains, and why it is being used. That allows organizations to share data widely while exposing it precisely.
This is also where Immuta’s “write once, enforce everywhere” model matters. Policies are written against metadata and tags, so they scale across platforms and new data inherits protection automatically. That helps organizations avoid role explosion, brittle views, duplicate tables, and policy rewrites as environments grow.
How delegated authorization works
Another key part of the model is delegated authorization. The agent acts on behalf of the user, not as the user. Access decisions reflect the combination of human entitlements, agent entitlements, and active data controls, with purpose or context where applicable.
That distinction is important because it preserves both control and accountability. It avoids identity borrowing, reduces the risk of rights inflation, and keeps the agent’s identity distinct from the human’s identity. Organizations can let agents be useful without collapsing human and agent access into one undifferentiated set of permissions.
How Immuta supports temporary elevated access
Sometimes the first governed answer is not enough. A user may need access to a masked field or an additional dataset to continue an investigation or answer a follow-up question.
That is where the broader provisioning model matters. If policy already covers the need, access can be granted automatically. If not, Provision by Request provides a governed workflow for exceptions, with automation and human oversight where needed. This allows organizations to handle predictable access, governed self-service, and agent-driven actions within the same provisioning model.
The value here is not just flexibility. It is controlled flexibility. Immuta’s policy exceptions are designed to be explicit, time-bound, and auditable, which helps organizations support legitimate needs without letting temporary access turn into permanent privilege expansion.
How Immuta audits the agent and the human together
Immuta’s agentic model supports dual-identity audit, capturing both the human who initiated the request and the AI agent that acted. It is designed to answer three essential questions clearly: who asked, what acted, and why.
That is a major improvement over the agent authenticating as the user. When an agent simply logs in as the user, logs can make it look like the human executed the action directly. With Immuta’s model, the record preserves both truths at once: the human asked, and the agent acted under a governed, temporary access model. That strengthens forensic clarity, compliance defensibility, and accountability.
Immuta also centralizes auditing across platforms, with visibility into who accessed what, when, and why. That gives organizations a clearer path to continuous compliance without having to stitch together logs manually from multiple systems.
Why this matters now
AI agents are becoming a new class of data consumer, and enterprises are moving from AI pilots to production. At that point, access becomes the limiting factor. The challenge is no longer just protecting data. It is delivering the right data safely, quickly, and provably to both human and non-human consumers.
That is why governed access matters so much right now for prospects, customers, and strategic partners. This is not just about making one demo work. It is about giving organizations a model they can rely on as agent-driven interactions scale across analytics tools, cloud data platforms, catalogs, and conversational interfaces.
The bottom line
Enterprise AI needs more than a powerful model. It needs governed access to data.
With Agentic Data Access, Immuta extends data provisioning to AI agents through temporary role vending, fine-grained policy enforcement, delegated authorization, and dual-identity audit. The result is policy-driven, temporary, auditable access at machine speed, without impersonation, standing privilege, or ticket-driven delays.
