Data use agreements (DUAs) are vital to ensuring individuals’ data is used compliantly and transparently. Just as data use agreements help protect data subjects’ personal privacy, avoiding misuse of personal data can protect organizations in every sector, from healthcare and financial services to the government, from liability, fines, breaches of trust, and reputational harm.
In defining contractual obligations for how sensitive data will be transferred and used, organizations commit to restricting the use and disclosure of personal data. But translating DUAs into policy can be ambiguous and challenging for data engineering and operations teams.
For Snowflake users, Immuta helps close the gap between DUAs and policy enforcement with Snowflake compliance and audit reports for data use agreements.
Challenges to Secure Data Sharing
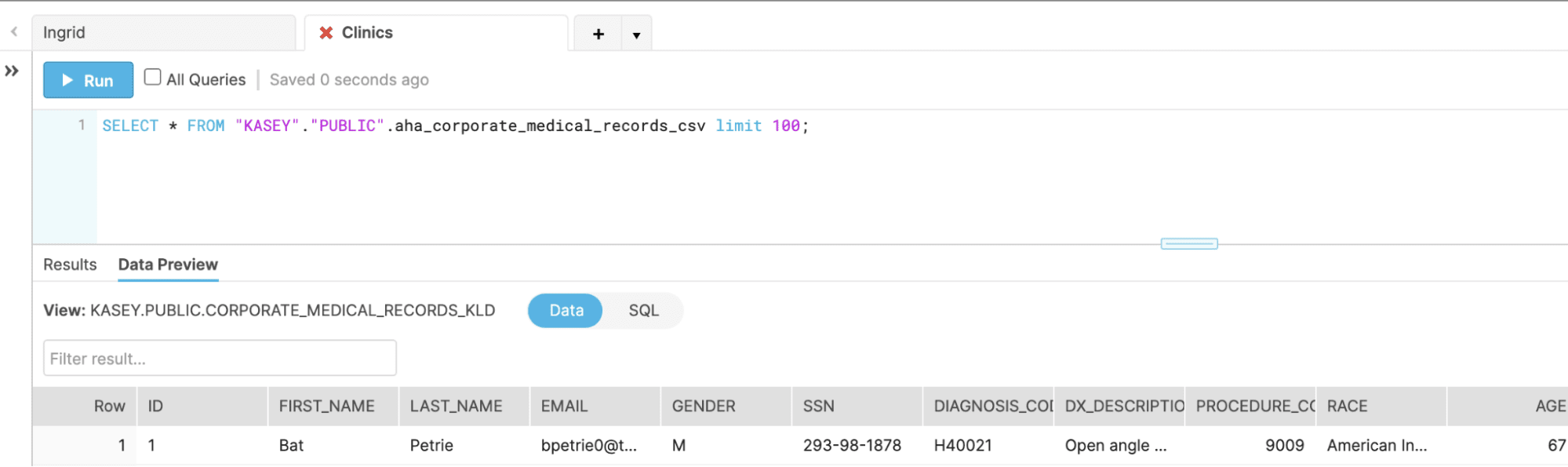
Data use agreements are extremely common in the healthcare industry, as requirements of HIPAA’s privacy rule. For purposes of example, let’s assume two researchers, Ingrid and Harry, are collaborating on a project using Snowflake as their data warehouse. Ingrid is an admin in Database_Clinic1, while Harry has admin privileges for Database_Clinic7; FLU_Vax is a separate database to which they both have access via a specific role called Project_FLU_Vax. The project requires data from both Clinic 1 and 7, and therefore has reference permissions on both databases.
When Ingrid creates a view in the Project_FLU_Vax database, Harry can see it, and vice versa. However, this scenario means that Ingrid and Harry are responsible for isolating the data that they think should be included in the project, which could lead to exposure and use of too much or too little data — which could either put the project in violation of HIPAA guidelines or stifle the ability to draw meaningful insights from the data. By tying roles to views, they are setting up a proliferation of roles that can become unmanageable, inefficient, and risky. Ultimately, it is very difficult to prove compliant data access and track down violators to the data use agreements.
Implementing Snowflake Attribute-Based Access Control
To minimize the imminent proliferation of roles in this scenario, you need to implement attribute-based access control, which leverages user and data attributes to drive data access policies. Instead of creating a common role (Project_FLU_Vax), you assign a relevant and global attribute, ClinicID, but specify its value relative to the user’s main clinic — Ingrid sees records where ClinicID=1 and Harry sees records where ClinicID=7.
Immuta’s native integration with Snowflake allows Snowflake data to be easily registered in Immuta and tagged for direct identifiers, indirect identifiers, and other sensitive attributes. Once the data set has been registered, you apply a global policy that filters rows so that ClinicID matches the value in the column ID. Now, when a query is run in Snowflake, Ingrid will automatically see records where ClinicID=1 and Harry will see records where ClinicID=7. This is in contrast to Snowflake’s object tagged role-based control model that requires management of predefined roles and user mappings.
Assigning Purpose-Based Access Control to Data Use
In order to collaborate as efficiently as possible, Ingrid and Harry need to be able to work together on a common set of data — and they need to be sure that data is being accessed and used compliantly, in accordance with the DUA. How is this done if their attributes are such that each sees a different clinic’s data?
Immuta enables data teams to work together under a special declared purpose. This can be accomplished by creating a collaborative space used for special data analytics and data sharing initiatives that allows group members to collaborate on specific data sources, bound by a common purpose and defined policies. In Immuta, this capability is called a Project. These defined policies allow for access to data for a narrowly defined reason, which is a requirement of major regulations like HIPAA and GDPR.
When a purpose is assigned to the project, data access is equalized, meaning the data set is limited to the lowest common denominator of accessible data. So, if Ingrid had permission to see PII but Harry did not, both Ingrid and Harry would see records with PII hidden. Data equalization helps prevent unauthorized access in a data sharing scenario. Declaring a purpose for the data use carves out an exception for data access within that project, and legal and compliance teams are able to incorporate legal language into the purpose statement to help draw a direct line of sight from DUAs or regulations to access control policies. Essentially, this adds a layer of assurance to Snowflake compliance and auditing by creating transparency and accountability at both the front end and back end.
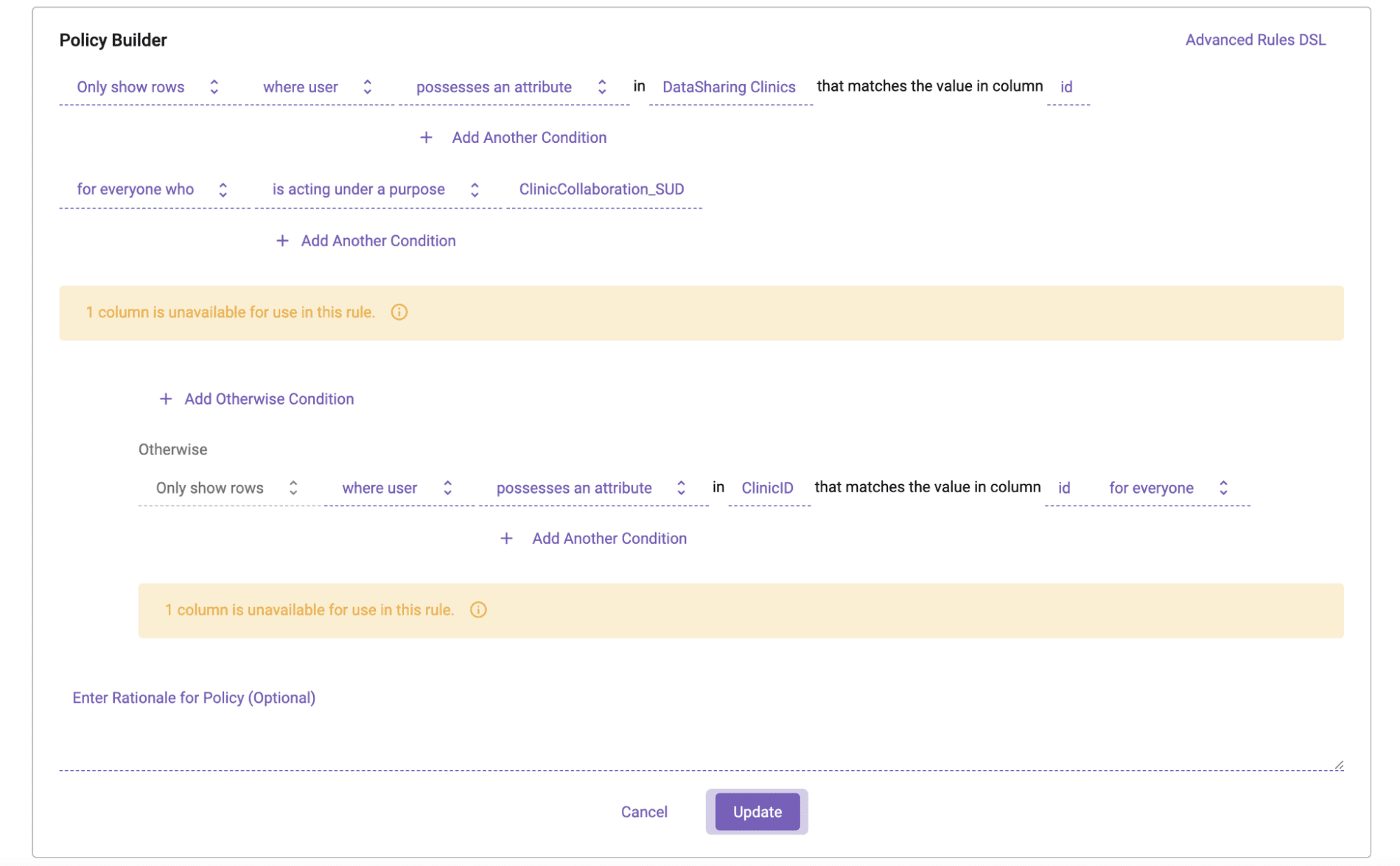
In practice, Ingrid and Harry would be assigned an attribute, DataSharingClinics, and the purpose would be assigned as ClinicCollaboration_SUD, as shown here:
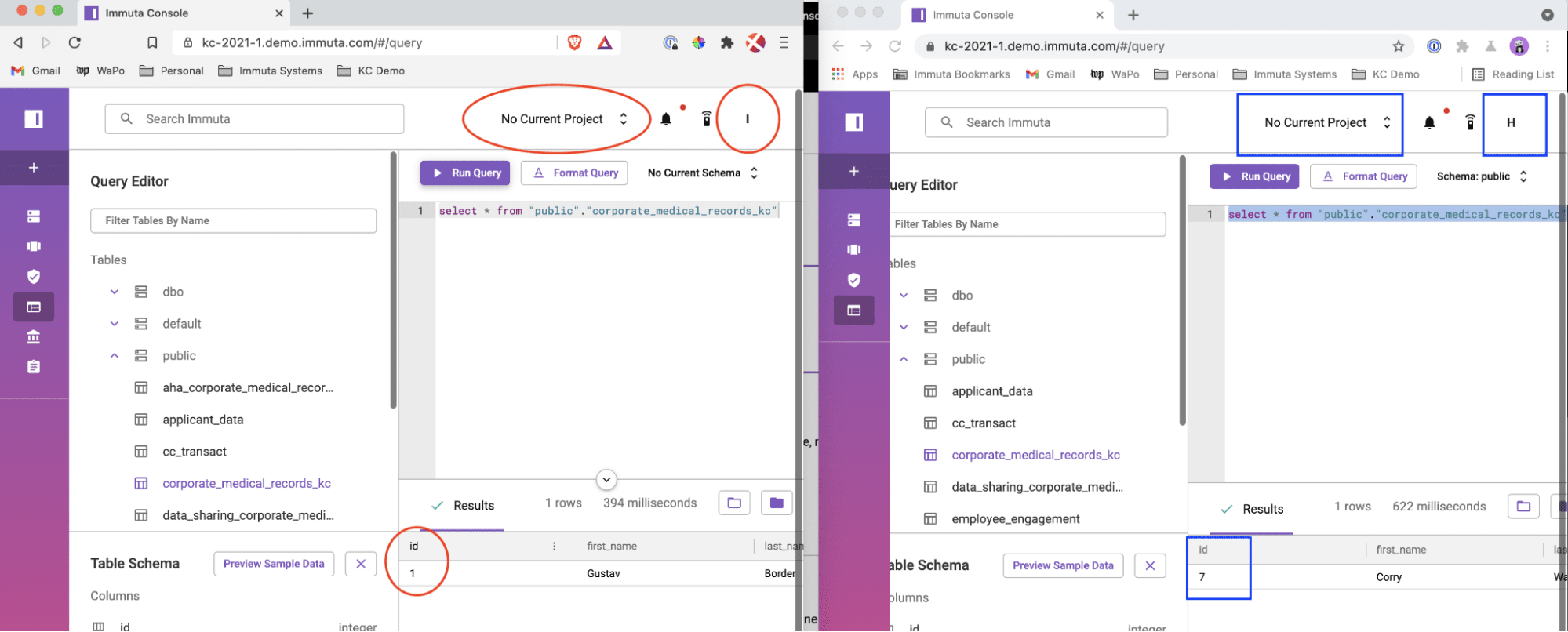
Once collaborators have accepted the purpose statement and the project context has been declared, let’s look at how the same query will return different results. Here, Ingrid (on the left) and Harry (on the right) are not working under a specific project; therefore, when Ingrid runs a query she only sees records for Clinic 1, while Harry only sees Clinic 7 data.
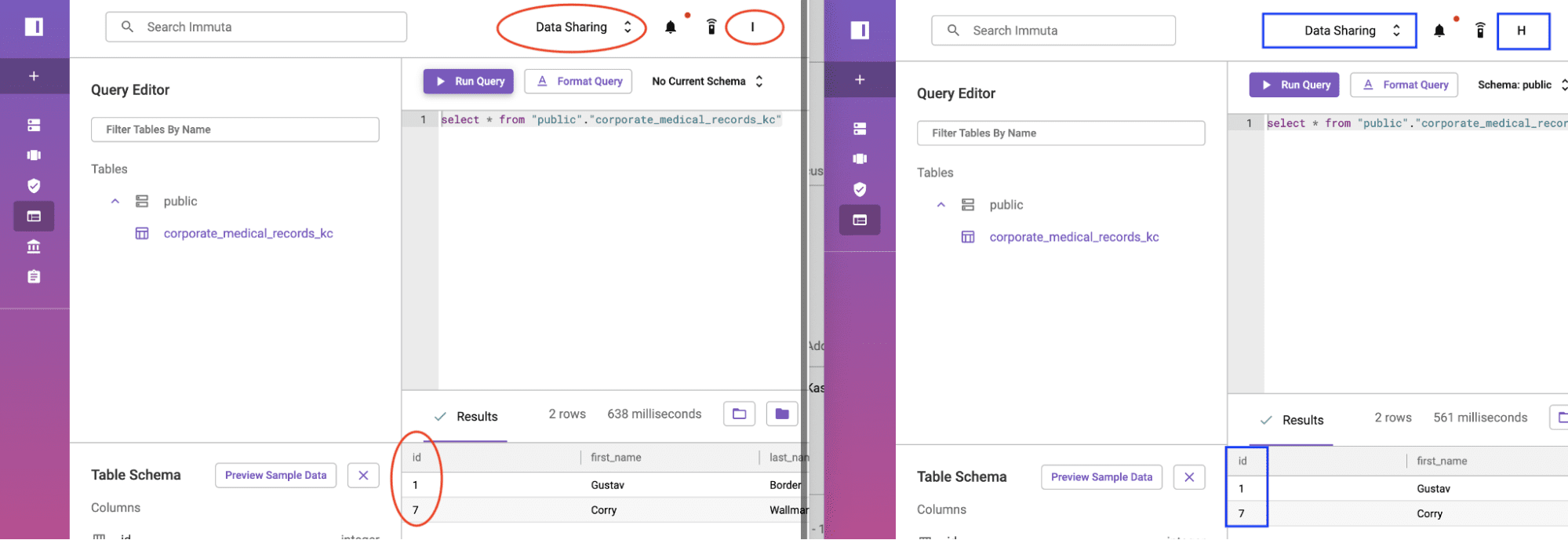
When the purpose changes, however, they are both able to see data for Clinics 1 and 7.
Note that all UI operations can also be done programmatically “as code” in Immuta, and all policies are enforced transparently to Snowflake users without any performance overhead.
Snowflake Compliance & Auditing for Data Use Agreements
By creating a single global data policy and updating specific attributes, Immuta enables dynamic data sharing to account for all data use agreements and rules. When conducting an audit on DUAs, legal and compliance teams are able to use Immuta’s automated reporting and data audit trails to substantiate that anyone who accesses specific data has an appropriate purpose for doing so, as well as every user subscribed to a data set, who queried data when, and what the specific queries were.
Controlling access at the front end and being able to easily audit it on the back end through Immuta helps organizations in every sector substantiate appropriate data sharing and use. Immuta Projects enables secure data sharing and collaboration, so data teams can efficiently access and use data, and accelerate speed to insights. This also helps mitigate liability for unauthorized access and avoids having to reverse engineer data usage in order to prove compliance with data use agreements, or track down responsible parties for violations, which can require substantial time and overhead.
To see how to enable secure data sharing and auditing for data use agreements with Immuta’s native Snowflake integration, request a demo.